SecVSC Uer’s Installation and Operation Manual
Brief Introduction to the Installation and Use of SecVSC Product
(SecVSC Personal Edition V1.4.2)
| Item | Product Package | Version | Description |
|---|---|---|---|
| 1 | -VSC-IssuingP -SecureLogon | V1.4.2 | SecVSC Personal Edition (PC) with certificate issuance management tool and basic PKI secure logon component |
| 2 | -SecVSC App | V1.4.2 | SecVSC personal version (mobile version), including Android and iOS |
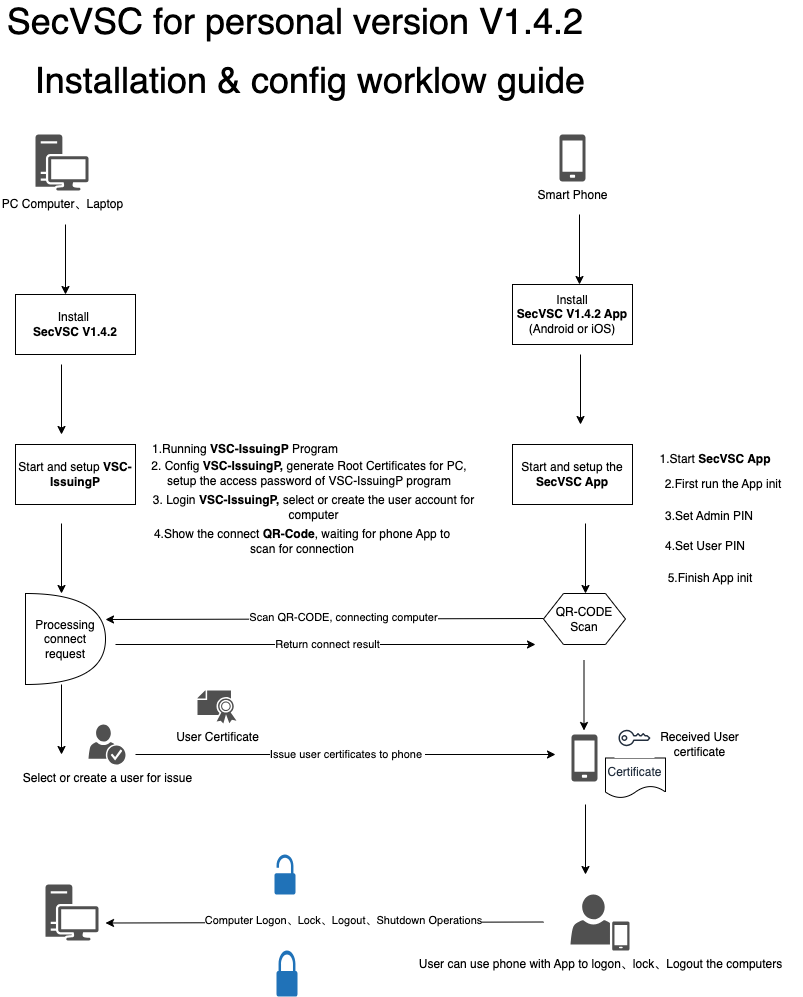
1. Overview of installation and configuration process
Personal version of SecVSC V1.4.2 product is located in a single terminal host device multi-factor security authentication system login, can be configured through the policy to set up a single device computer user multi-factor authentication security login, personal version of the simplification of the management of the software system configuration and deployment of the complexity of the system can meet the windows system environment of various types of stand-alone use: Windows 10 series and Windows 11 series, and Windows Server.
The personal version of SecVSC V1.4.2 product allows one computer terminal to deploy a standalone version, and one computer terminal is allowed to log in and access authentication of 3 user digital certificates by default, and different user certificates can be installed on one cell phone, or different user certificates can be installed on different cell phones respectively.
The general description of the installation and configuration process for the Personal Edition SecVSC V1.4.2 product is shown below:
1.1 System environment of SecVSC for personal V1.4.2 products
| PC computer | Smart Phone | |
|---|---|---|
Microsoft Windows 10 series operating systems; Microsoft Windows 11 series operating systems; Microsoft Windows Server 2016 or above | Android | iOS |
| Android version 8.0 or above | Apple iOS version 10 or above | |
1.2 Hardware environment requirements of SecVSC for personal V1.4.2 products
| PC computer | Smart Phone | |
|---|---|---|
| Android | iOS |
| Bluetooth Low Energy (BLE) 4.0 or above. | Bluetooth Low Energy (BLE) 4.0 or above. | |
2. Software installation and configuration instructions
2.1 SecVSC software installation steps and configuration instructions for PCs
2.1.1 Software installation process on PC
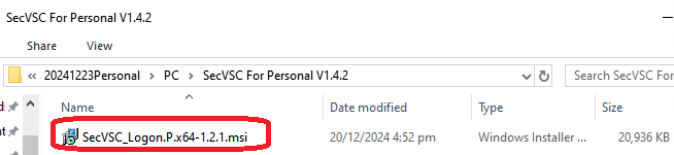
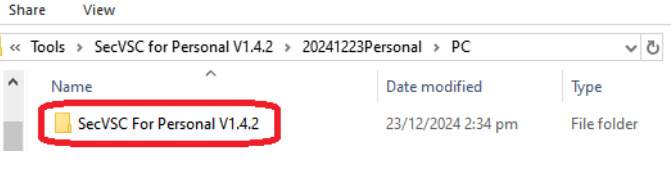
(1) Open the “SecVSC For Personal V1.4.2” installation package directory:
(2) Click on the “SecVSC_Logon.P.x64-1.2.1.msi” installation file to install SecVSC For Personal V1.4.2 on your computer:
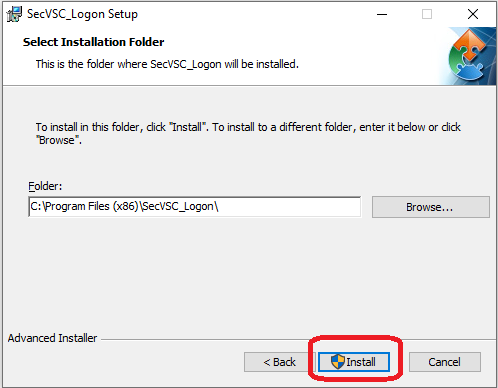
(3) When the installation screen appears, click “Next” to continue installing SecVSC for Personal:
You can follow the prompts and select the appropriate installation path to install it on your computer.
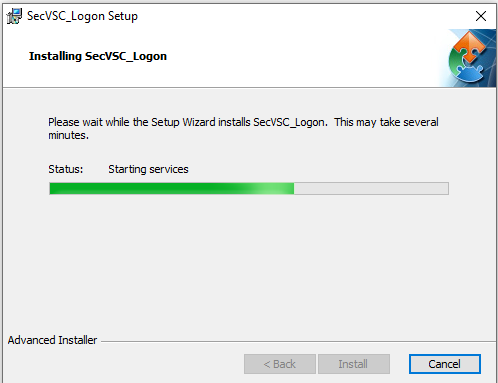
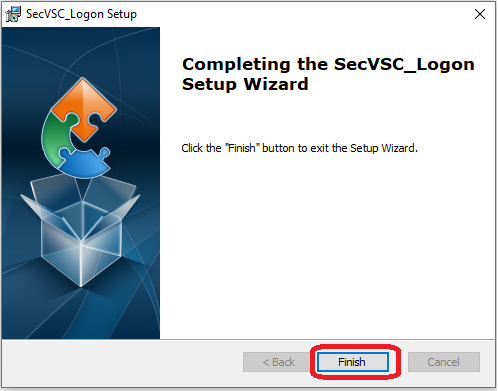
(4) After the installation process is complete, click the “Finish” button according to the prompts to complete the installation of the software on your computer.
The above steps to complete SecVSC For Personal PC software installation, this installation includes VSC-IssuingP certificate management tool and SecureLogon security components.
2.1.2 Computer-based software configuration process and instructions
After the installation of the software on the computer side is completed, it is necessary to carry out the initialization and configuration work for the first time use, the specific steps are as follows:
Select the “VSC-IssuingP.exe” certificate management tool on your desktop or in an application program and click Run:
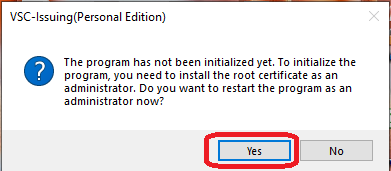
Click Run VSC-IssuingP Certificate Management Tool. When you run it for the first time, the software prompts you to make the appropriate initial configuration:
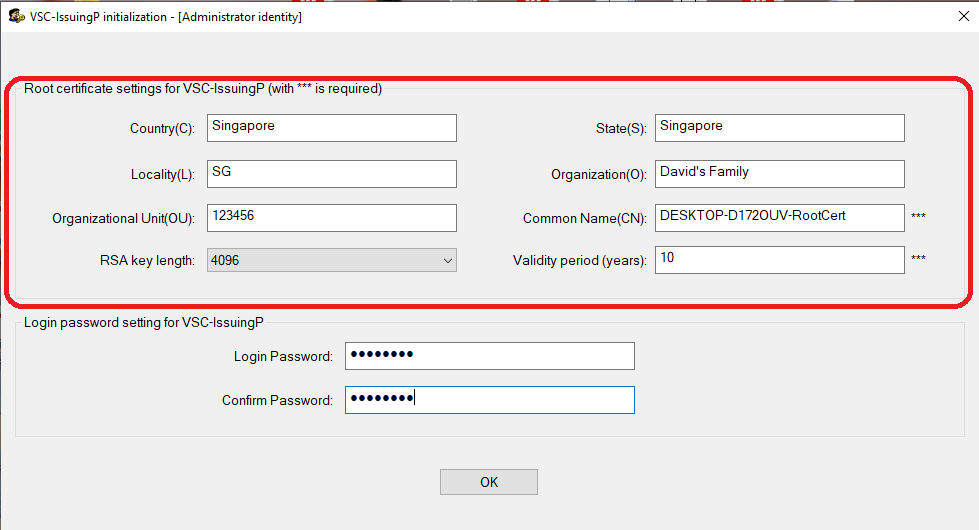
The system prompts you to enter the initialization interface, you need to generate a local root certificate for the installed computer and set the login password for the VSC-IssuingP certificate management tool (administrators can log in to this tool software through the password for certificate management):
The administrator can set the information related to the root certificate, as shown in the red box in the above figure, you need to enter the corresponding certificate content and parameters, the specific content is as follows.
Country: Country Name;
State: The State;
Locality: Locations;
Organization: Name of the Organization or Institution to Which One Belongs;
Organizational Unit: Organization code;
Common Name: Common name, usually without modification, by the software automatically according to the computer name of the corresponding common name generation, as shown in the figure above, DESKTOP-D172OUV-RootCert for the software automatically according to the computer name of the common name, this name can be edited by the administrator in the initialization according to the actual need for editing and modification;
RSA key length: This is a definition and selection of the length of the RSA key, different key lengths can be selected, the default is 4096 bits;
Validity period(years):The validity period of the root certificate, where the administrator can define the validity period (in years) of the specific root certificate when generating the root certificate for this computer.
Note: In the parameter definition item of the above root certificate, the parameter item with “***” symbol must be inputted and set, while other parameter items can be left unfilled, depending on the administrator's specific management needs for root certificates.
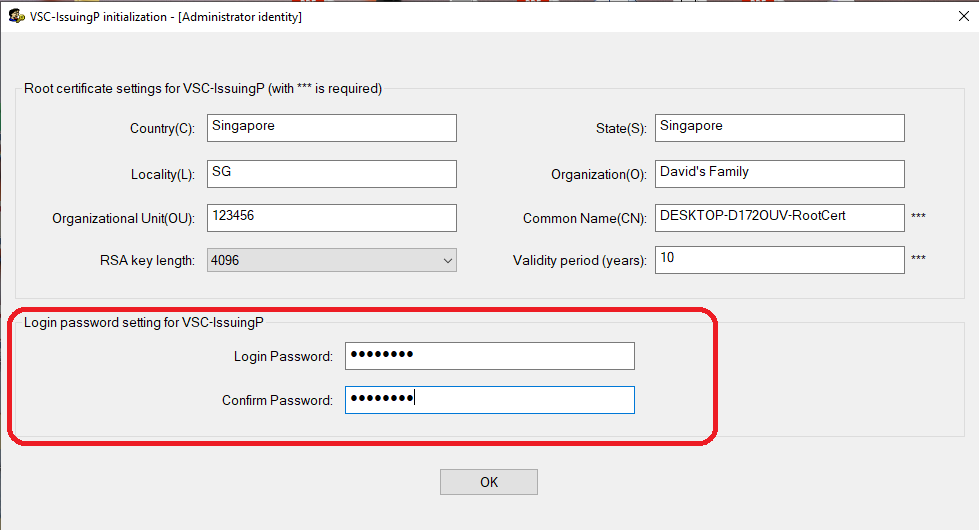
The lower part of the above figure, as shown in the red box, is to set the corresponding login access password for this VSC-IssuingP certificate management tool, which is usually set and used by the administrator.
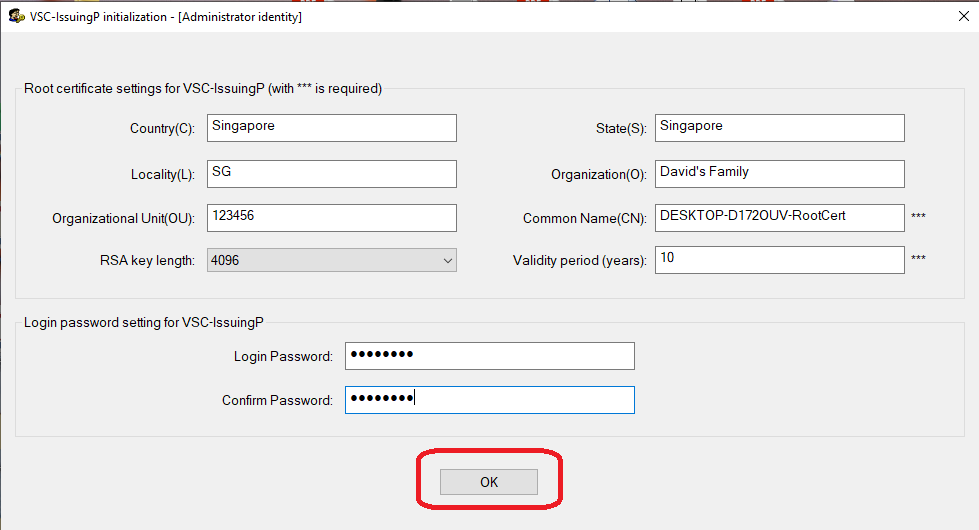
The administrator can enter the corresponding login password and confirmation password in the above settings, and click the “OK” button to generate the root certificate and initialize the configuration of VSC-IssuingP certificate management tool.
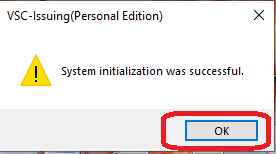
After the initialization of VSC-IssuingP is completed, the system will pop up the corresponding prompt dialog box, as shown in the following figure.
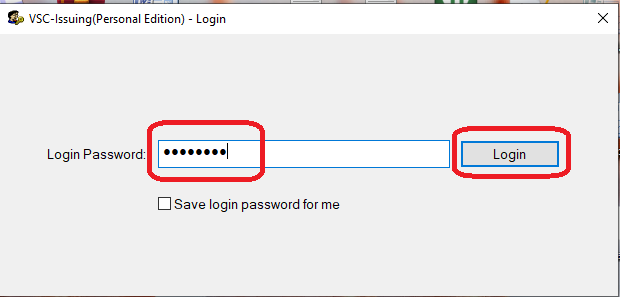
After clicking the “OK” button, complete the corresponding initialization work, re-run VSC-IssuingP, enter the login interface of VSC-IssuingP.
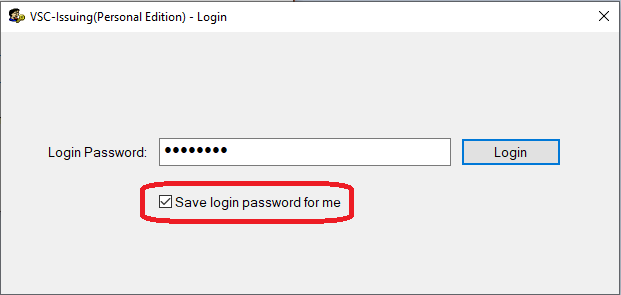
VSC-IssuingP usually requires a password for successful authentication. If you click the “Save login password for me” option, the system remembers the current password, so that every time you access VSC-IssuingP in the future, you can log in and use it without password authentication.
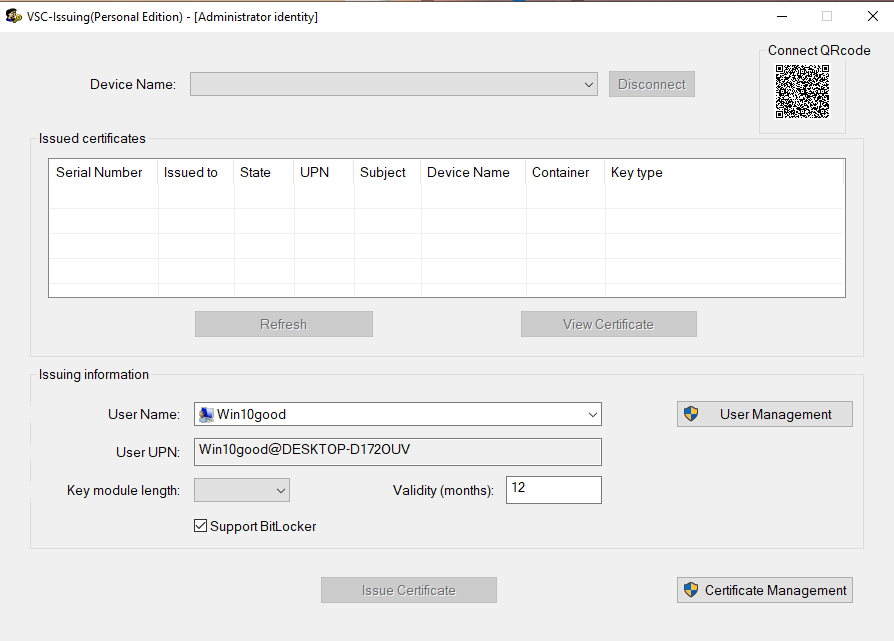
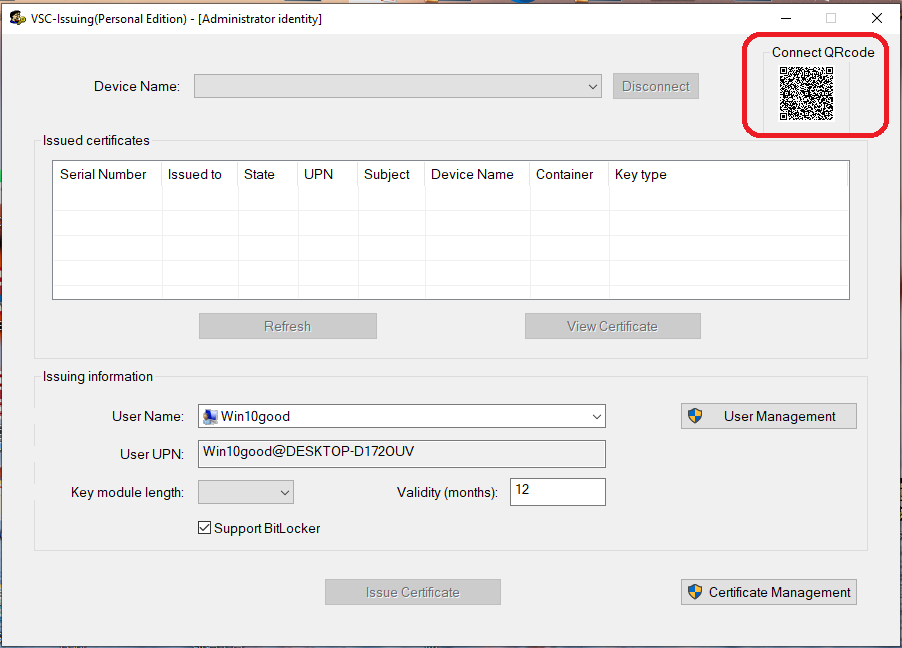
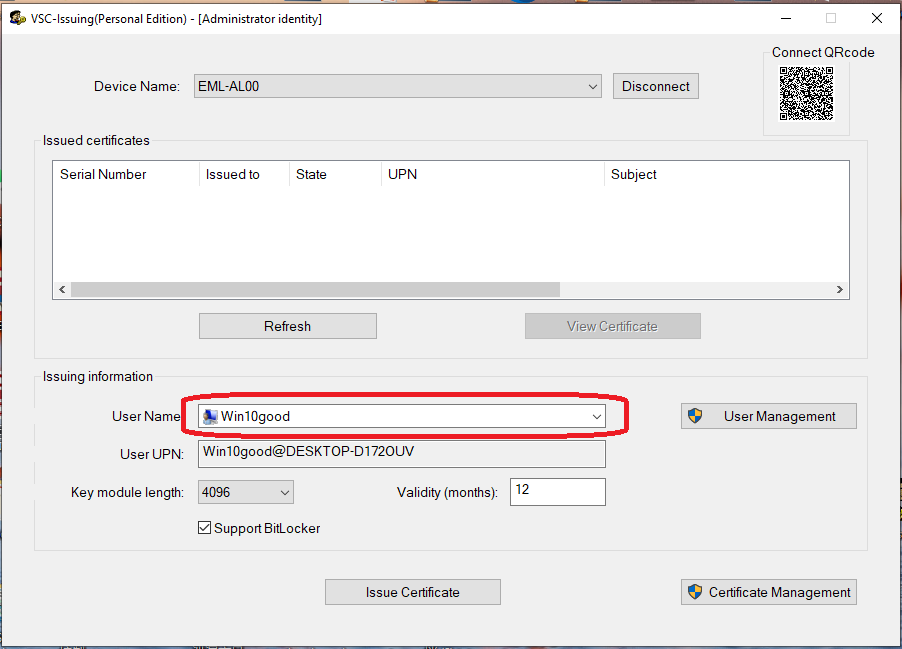
Enter the main interface of VSC-IssuingP Certificate Management Tool as shown below.
The main interface operation area above is provided for computer administrators to use to connect to specific cell phones (providing the computer side to connect to the appropriate QR-CODE, and the user's cell phone to scan the QR-CODE to connect to the computer through the SecVSC App on the cell phone side), as shown in the upper right side of the picture with the QR-CODE display;
The information and operations on the main screen are described as follows:
“Device Name:": This display box with a drop-down list is used to display the specific name of the connected device, usually the name of the cell phone device that has been successfully connected, if a computer is connected to a number of different cell phone devices, you can click on the drop-down list of the drop-down arrow to list and select the corresponding connected cell phone device; if the computer does not have a corresponding cell phone device connected successfully, the display box shows no information, as shown in the figure. If a computer is connected to several different cell phone devices, you can click the drop-down arrow to list and select the corresponding connected cell phone devices; if the computer does not have the corresponding cell phone devices connected successfully, the display box shows no information, as shown in the figure above;
“Connect QRcode": this displays the current computer's connection QR-CODE, if the computer's own Bluetooth function is normal, it will display the corresponding QR-CODE (computer mouse click on this small QR-CODE will pop up an enlarged QR-CODE, convenient for different cell phones to scan ), if the Bluetooth function of the computer itself is turned off or malfunctioned, the QR-CODE will not be displayed; this connecting QR-CODE is used to provide the cell phone device to be connected to the computer, scanning the QR-CODE through the SecVSC App installed on the cell phone device, and then clicking the “Connect” button in the App to activate the cell phone device. Click on the “Connect” button in the app to initiate the connection between the mobile device and the computer;
“Issued Certificates": This list displays an information box that shows the user certificates that have been written to the corresponding mobile device. If the mobile device connects to the computer successfully, the corresponding user certificates that have been authorized to be issued in the cell phone will be listed here, so that the administrator can check the user certificate issuance status of the specific mobile device that has been connected. The administrator can check the user certificate issuance status of the connected mobile device;
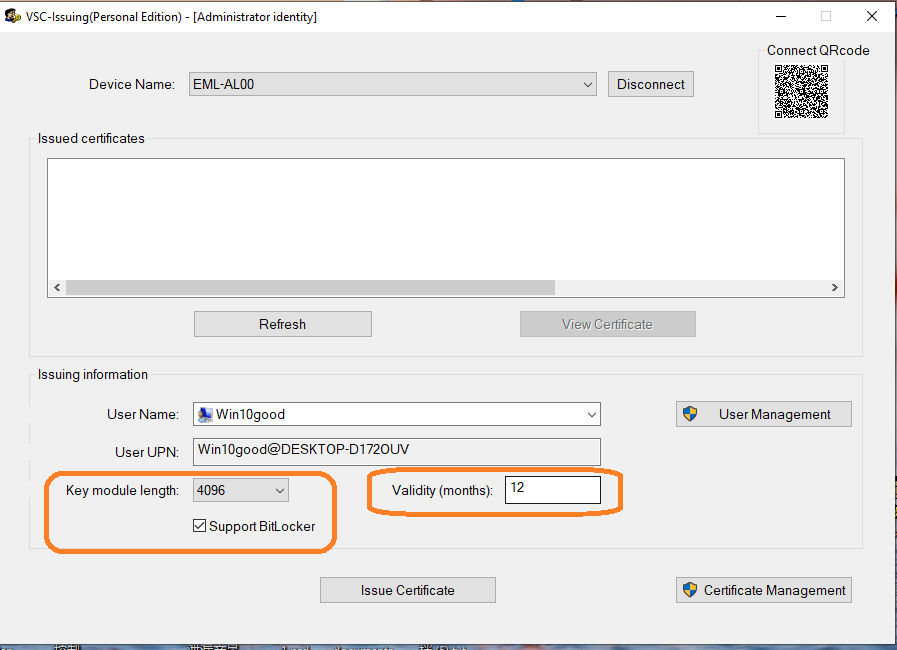
“Issuing information": this area is a user login account management function area, the administrator can select a specific user to issue the corresponding user certificate (authorized to write to the corresponding mobile device), if you need to add a new login user for the computer device, you can also click the “User Management” button into the user management function to carry out the corresponding new user operations; in addition, when the administrator selects a specific user account ready to issue certificates, you can specify the corresponding certificate key length (Key module length) and certificate validity period (Validity), the administrator can select a specific user to issue the corresponding user certificate (authorization to write to the corresponding mobile device). Validity), as shown in the above figure, the administrator can select User Name: “Win10good” user account, select the key length of 4096 bits, as well as the validity of the certificate for 12 months, and then issue the user certificate to the specific cell phone device;
2.1.3 Software license registration and activation process for SecVSC For Personal
Preparatory Stage
Visit the official website:https://www.junkai-tech.com, register as an official user, then select to purchase the corresponding product license of SecVSC product. After successful payment, you can download or receive the correspondingProduct Key (Software License).
Ensure the SecVSC software (VSC-IssuingP) is installed correctly on the target computer device, and the device has a stable network connection(for online activation);
If not network then offline activation requires additional preparation of offline verification workflow like apply an offline code from JUNKAI-TECH and offline active the license by user).
Software License Registration
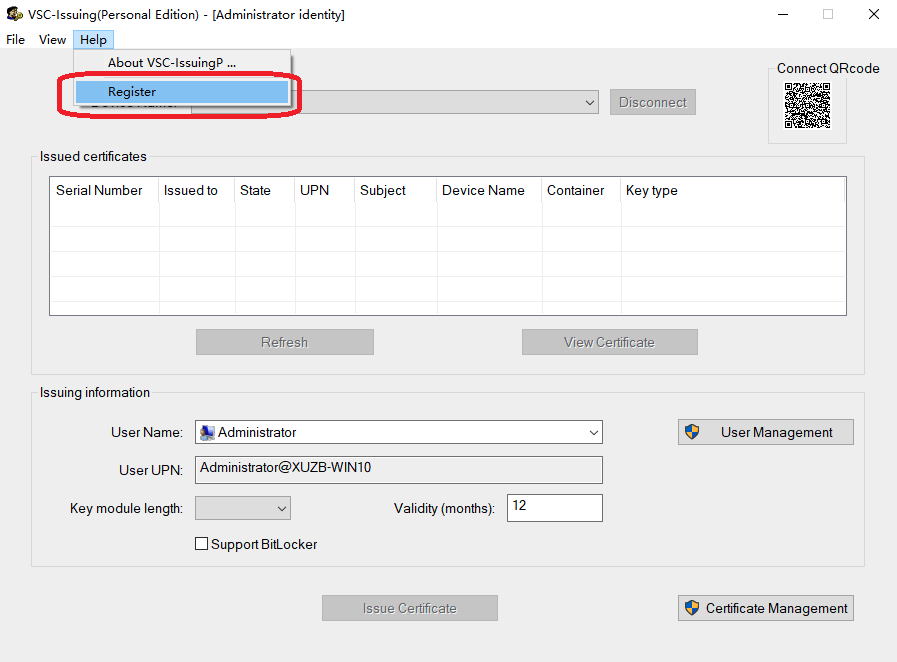
Launch the VSC-IssuingP program on computer site and navigate “Help” menu and click the “Register” sub-menu.
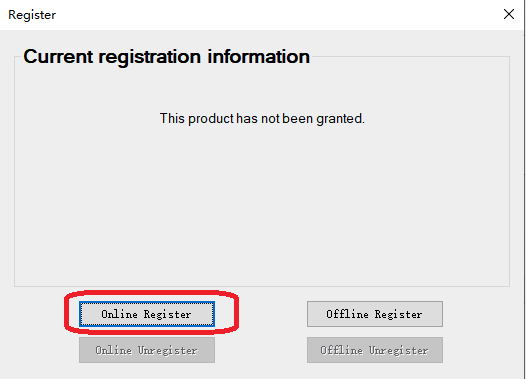
In the open 'Registration' dialog box, click the 'Online Register' button to start the online registration activation.
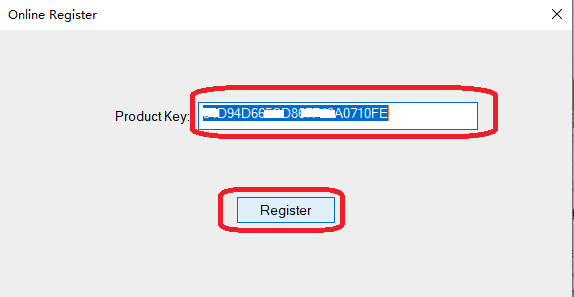
Enter the obtained product license Product Key, and then click 'Register' to activate online.
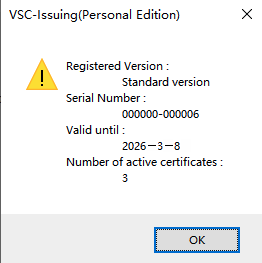
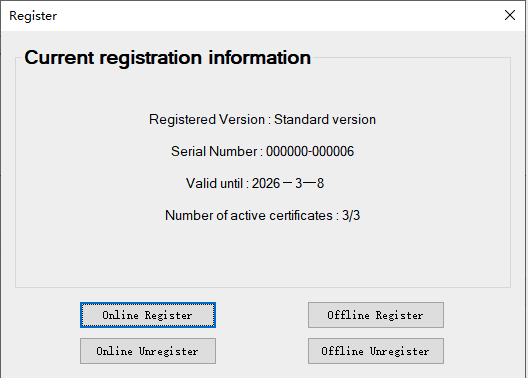
If the online activation is successful, the system will prompt the corresponding registration information, as shown below:
After successful registration, click the 'OK' button to close the current pop-up, and the complete registration activation information will be displayed on the 'Registration' page, as shown in the image below:
2.1.4 Process Description for Issuing User Certificates
After the VSC-IssuingP certificate management tool completes the corresponding settings, the administrator can issue the corresponding user certificates (written to the specific user's cell phone device) for the specific login user as needed, the specific process is as follows:
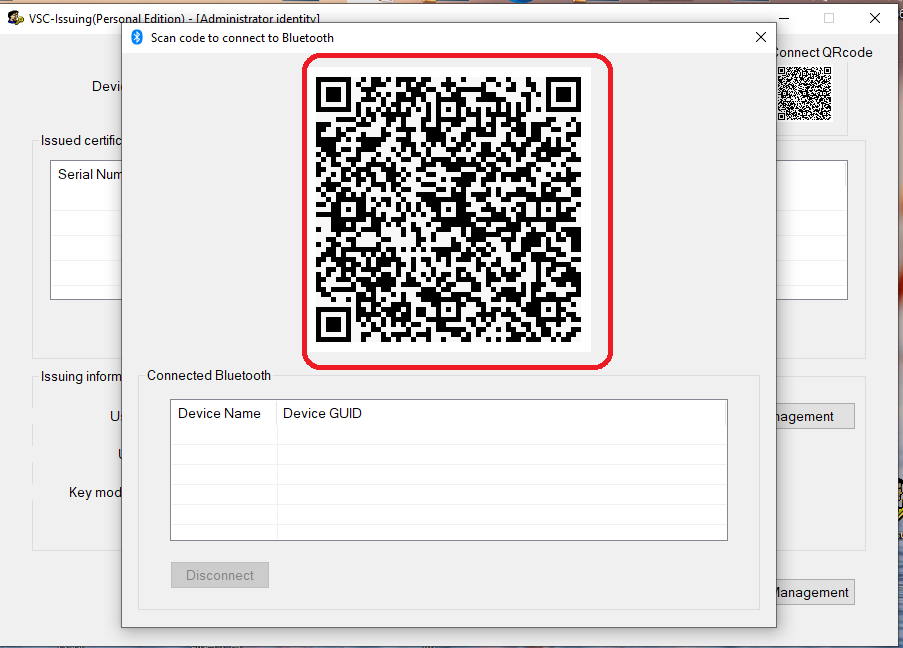
Administrator login to enter the main interface of VSC-IssuingP software, use the user's cell phone with SecVSC App installed, scan the connection QR-CODE on the computer side through the App to let the cell phone connect to the computer, as shown in the following figure:
You can connect directly by scanning the Connect QR-CODE on the upper right side directly through the mobile app, or you can click on the QR-CODE on the upper right side with your computer mouse to bring up the enlarged QR-CODE, and then scan the connection, as shown in the picture below:
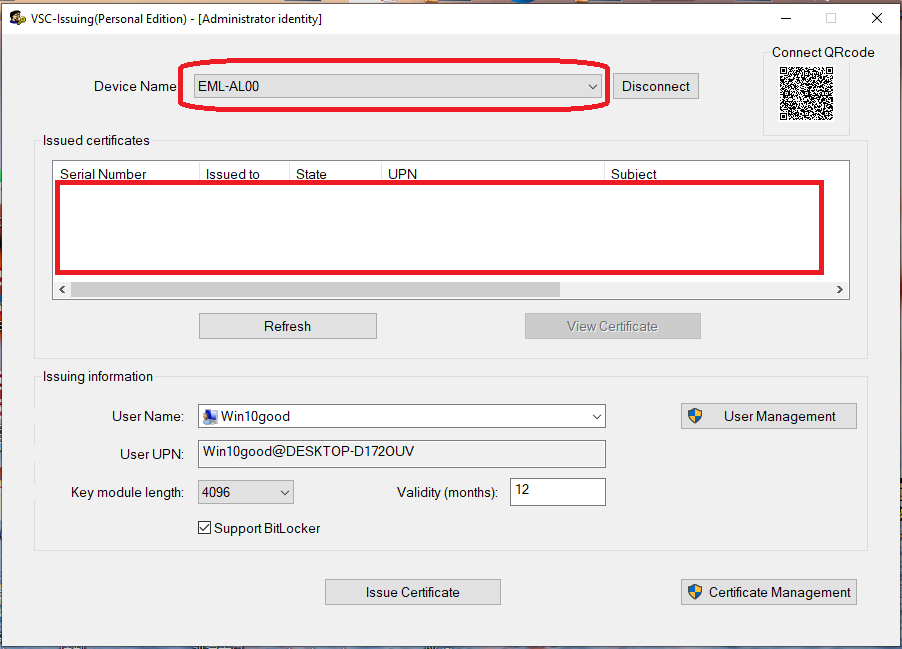
When the cell phone is successfully scanned and connected to the computer, the “Device Name” display box in the interface of VSC-IssuingP software on the computer side will show the name of the specific connected cell phone device, if there are more than one cell phone devices connected to the computer, the administrator needs to select the specific cell phone device for certificate issuance operation. If there are more than one mobile devices connected to the computer, the administrator needs to select the specific mobile devices to issue certificates, the following figure shows the connection of a new mobile device, you can see that there is no record of issued certificates in the “Issued certificates” list box, which indicates that the cell phone does not have any authorized certificate at the moment.
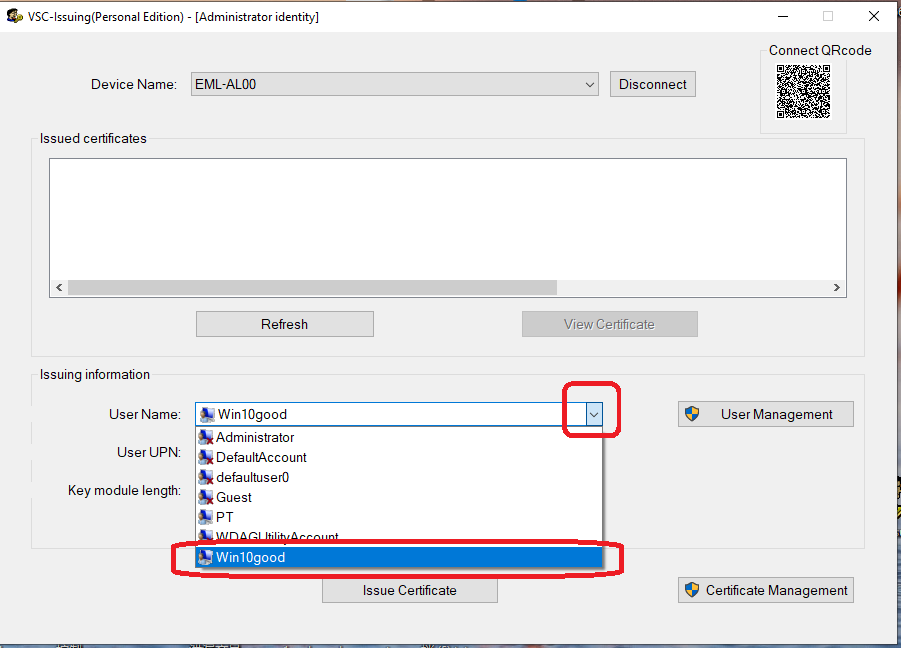
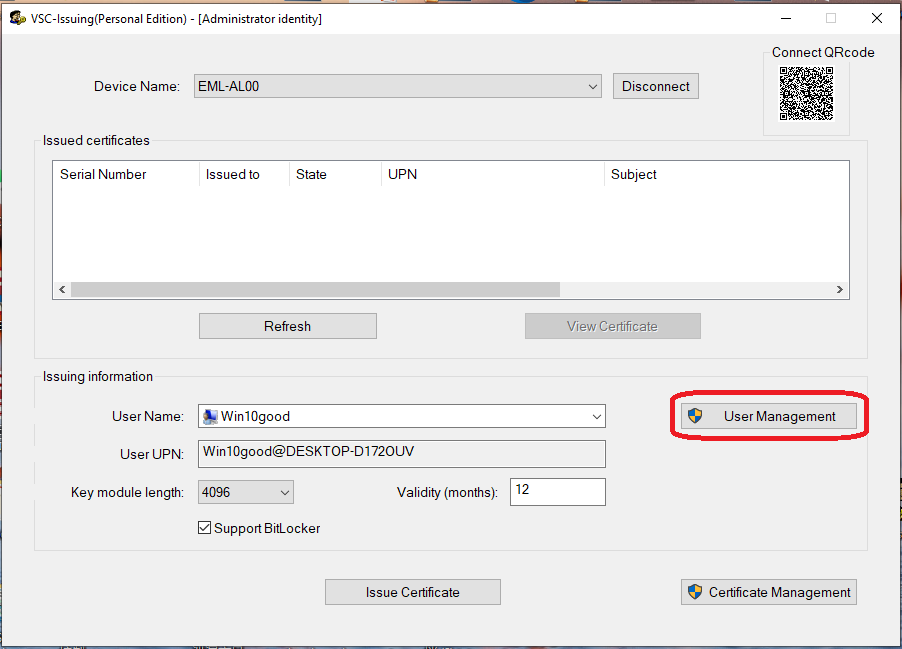
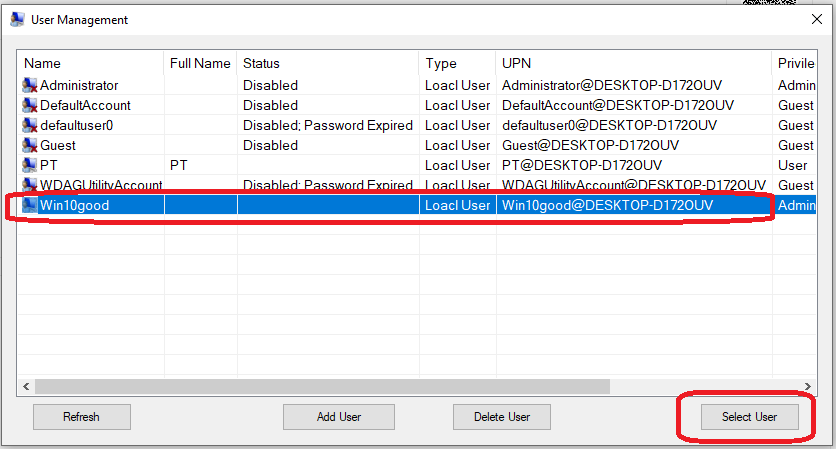
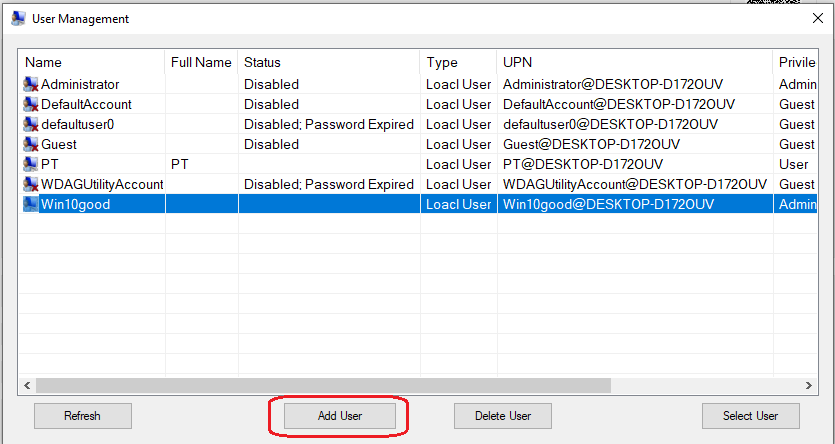
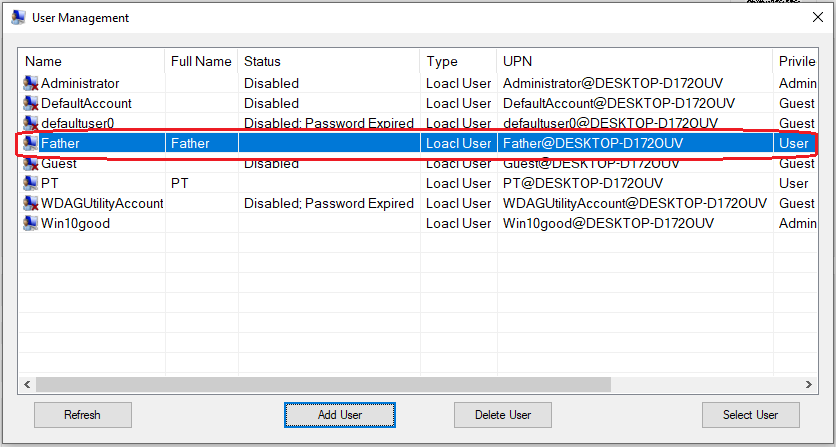
The administrator can now select the corresponding computer login user account to issue certificates, as shown in the following figure, you can directly in the “Issuing information” operation area of the “User Name” list selection box, directly You can directly select the corresponding login user account in the “User Name” list selection box in the “Issuing information” operation area (e.g. “Win10good”), or click the “User Management” button on the right side to bring up the corresponding user management dialog box to select the specific login user account (if you need to add additional login users, you can add them in the “User Management” dialog box on the right side). (If you need to add additional logon users, you can create a new logon user account by adding a new user in this dialog box), as shown in the following figure:
New users can be added by clicking the “User Management” button to bring up the corresponding user management functions for new users or user selection:
If you need to add a new computer login user, you can click “Add User” to add the login user, as shown below:
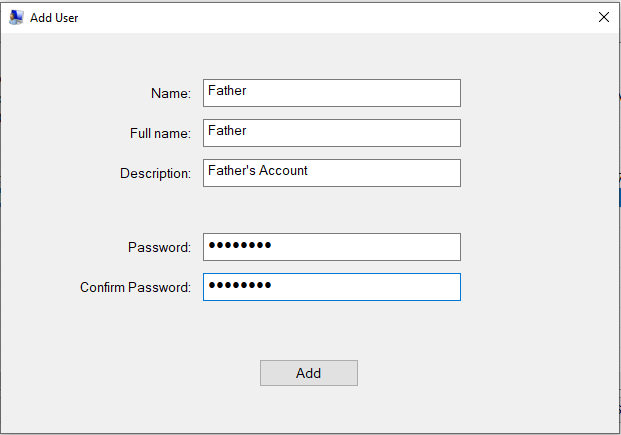
To add a user you need to enter the appropriate name, login password login information to create a new login user account, for example: If the family computer administrator is mom, and now you want to add a computer login user account for dad, you can add a user account named: Father, as shown:
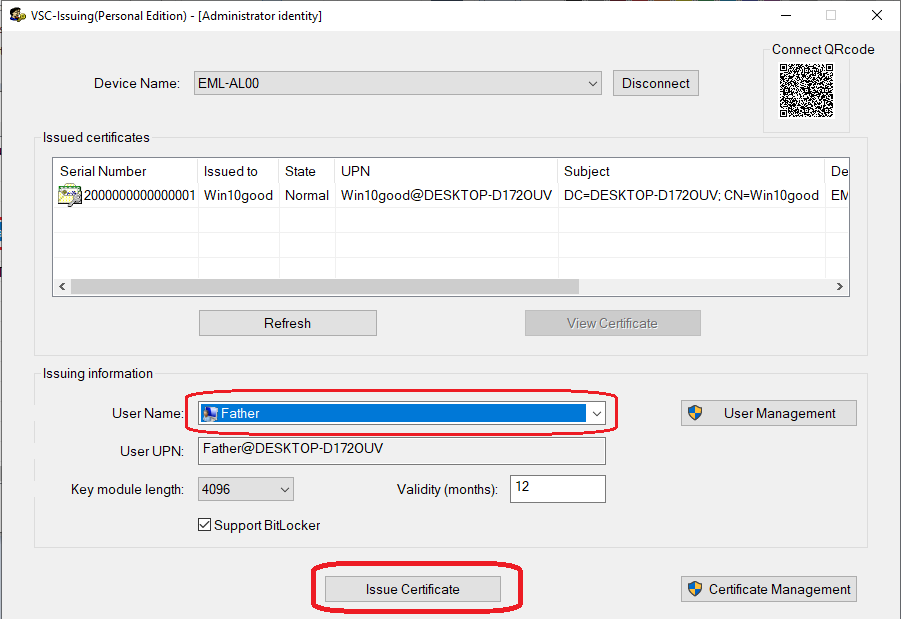
After adding a new login user account, the administrator can issue the appropriate user certificate for that user to write to that user's mobile device:
The example below shows that a user certificate named “Father” has been issued to Dad's cell phone device.
(4) After selecting a specific login user account, you can set the key length of that user's certificate, e.g. 4096 bits, and the certificate validity period, e.g. 12 months, as shown in the following figure:
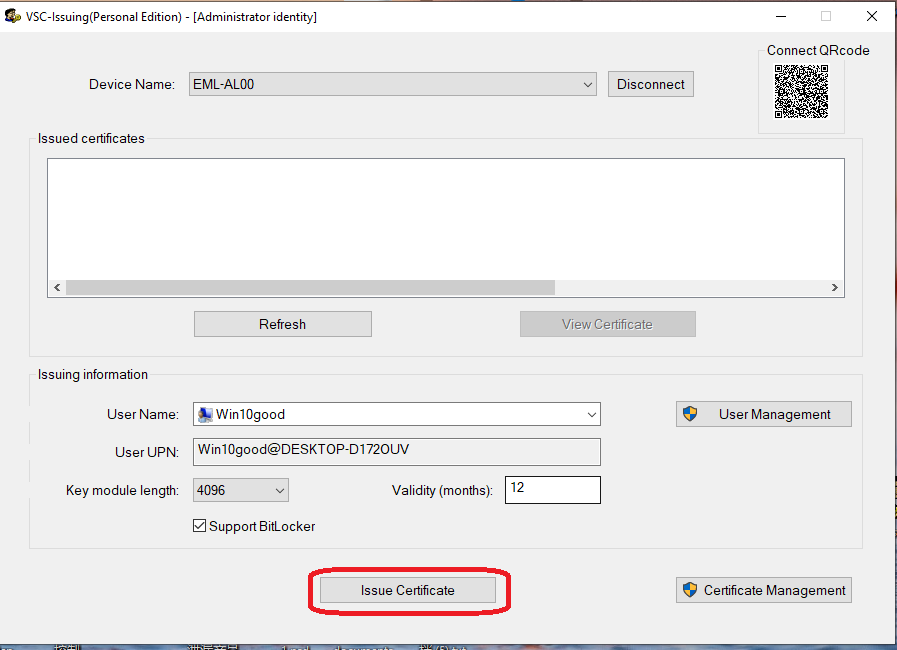
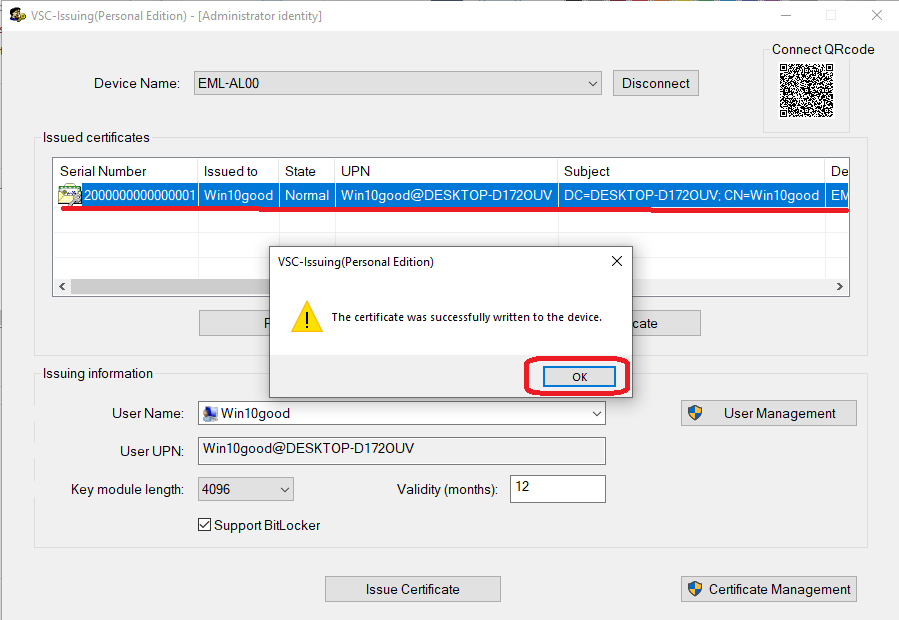
Click “Issue Certificate” below to issue the selected login user certificate to the specified user's mobile device:
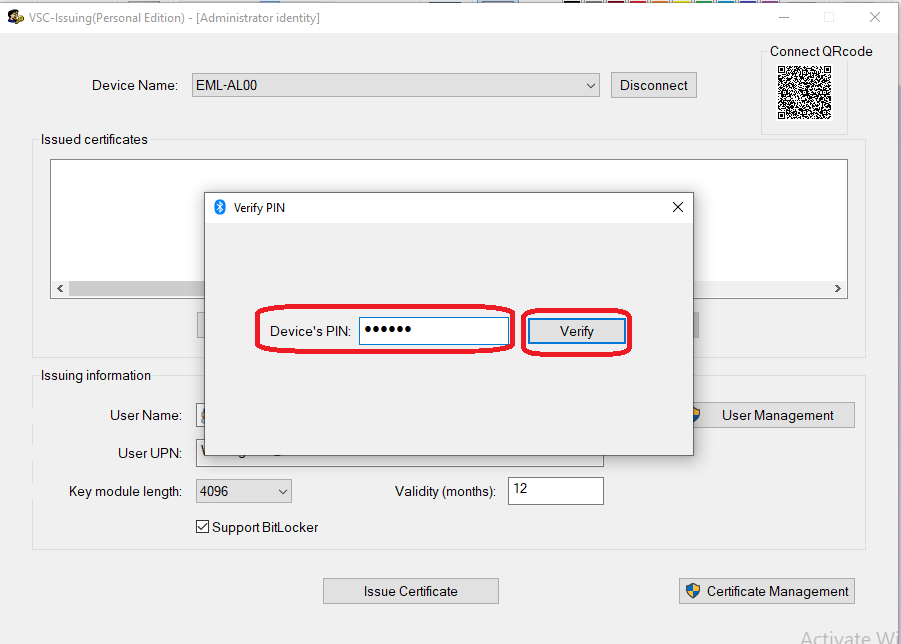
When clicking the “Issue Certificate” button to issue a user certificate, the software will pop up the corresponding “Verify PIN” dialog box, asking for the user PIN of the SecVSC app on the specified user's mobile device. At this time, the administrator can enter the user's PIN on the user's cell phone for verification, or directly click the “Verify” button to enter the user's PIN on the user's cell phone device (if the user's cell phone has already done the Verify PIN operation, then the certificate can be issued directly), and then the VSC will issue the certificate to the user. After successfully verifying the user PIN, VSC-IssuingP will issue the specified user certificate authorization to the corresponding mobile device:
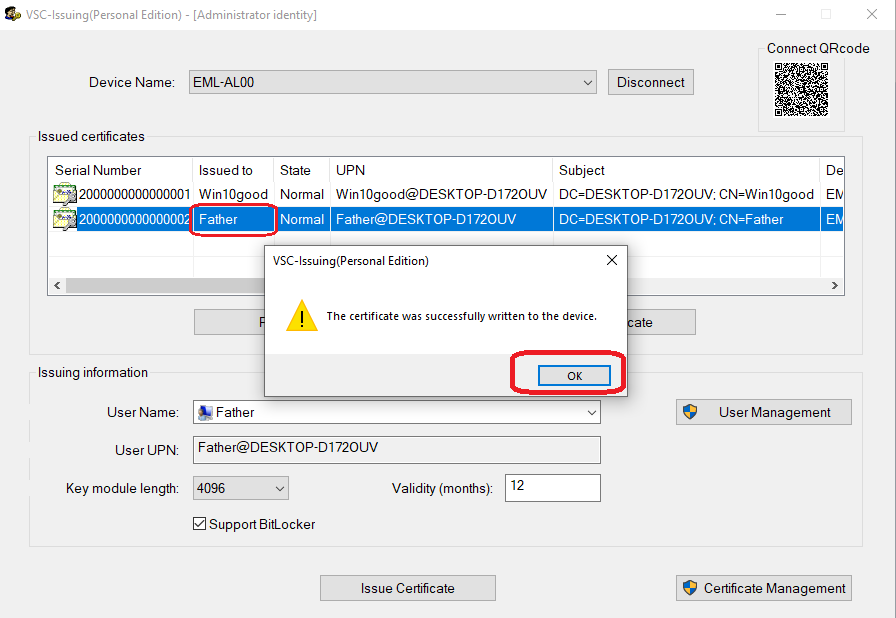
If the computer is connected to the phone normally, the relevant user certificate is written to the specific phone device, as shown in the following figure:
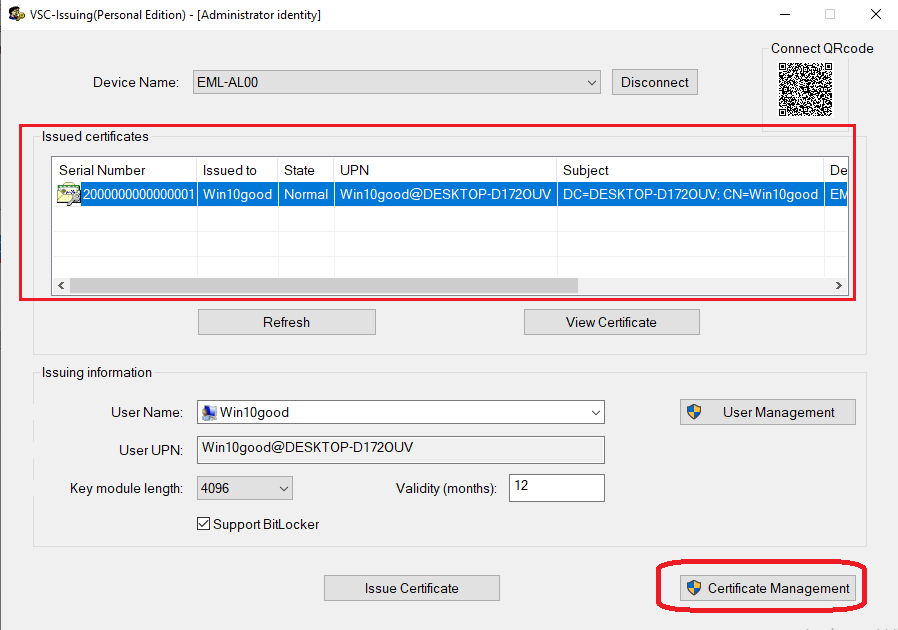
After the user certificate is successfully issued to the user's mobile device, the corresponding issued user certificate information can be displayed on the “Issued certificatres” list box of VSC-IssuingP software, as shown in the following figure:
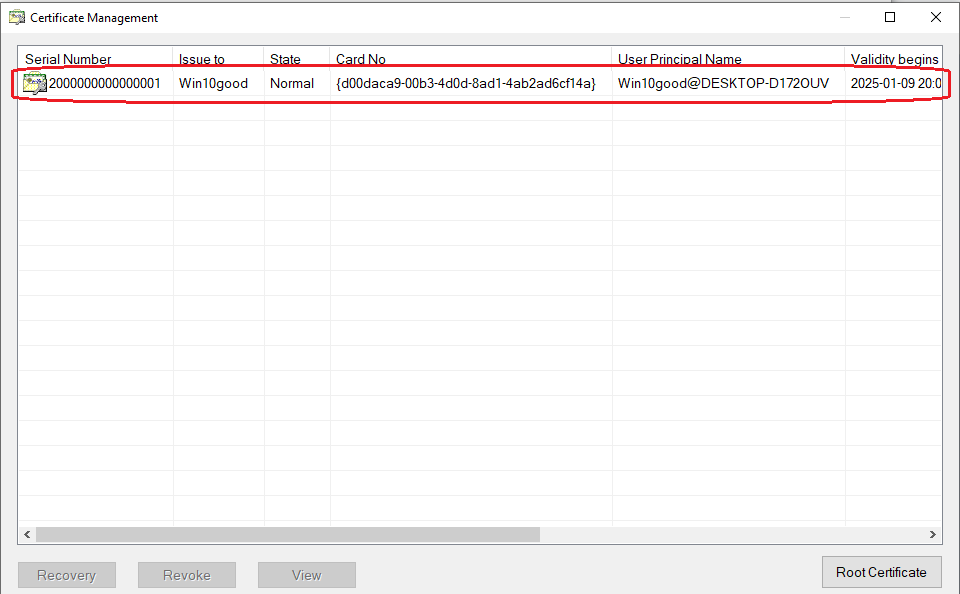
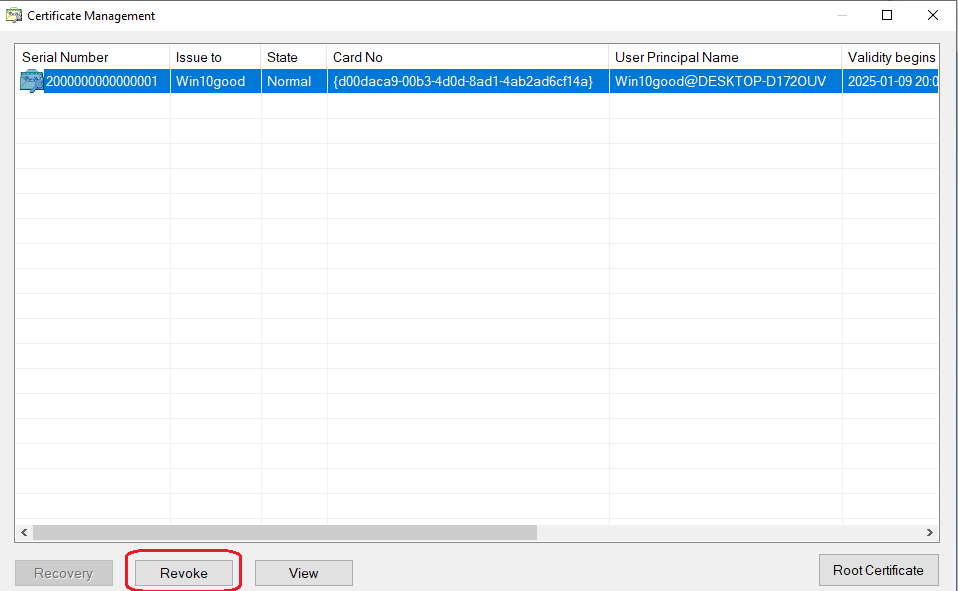
You can also click the “Certificates Management” button on the bottom right to enter the computer's certificate management function, the corresponding certificate view, certificate revocation and other operations.
Certificate Viewing, Certificate Revocation and Certificate Restoration
In the “Certificate Management” function dialog box, the administrator can unify and comprehensively manage all the issued user certificates of this computer, and there are three main operations:
View: View: Select a user certificate in the list to view it;
Revoke: Select a user certificate in the list for certificate revocation, if a user certificate in the computer is revoked, the mobile device holding the user certificate will not be able to be used for login security authentication on this computer;
Recovery: Select a user certificate in the list that has been revoked for certificate recovery, if the user certificate is recovered, the cell phone device holding the user certificate will be able to be used for login security authentication on this computer.
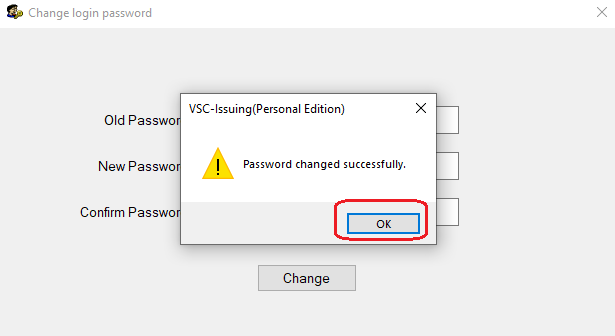
2.1.5 Change the login access password of VSC-IssuingP certificate management tool software.
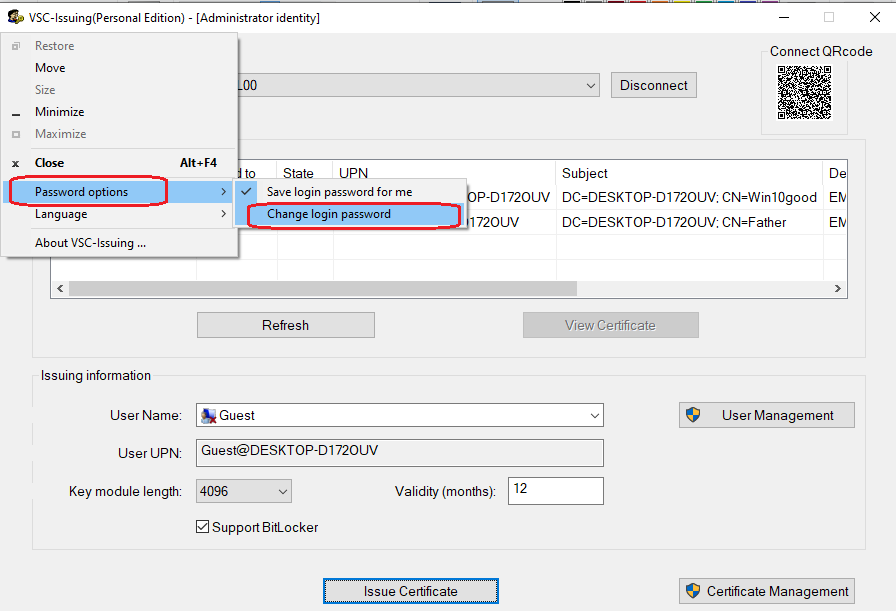
VSC-IssuingP certificate management tool is provided to the administrator of the computer for the corresponding computer device login access user certificate management software, in general the software can only be used by the administrator or the owner of the computer operation, therefore, login to the software need to carry out the corresponding software login password authentication, VSC-IssuingP software in the initialization of the initial setup needs to set the software access password, the administrator may also periodically change the software access password, change the login password operation is shown as follows VSC-IssuingP software needs to set the software access password in the initial setup of the first installation, and the administrator may also change the access password of the software periodically, and the operation of modifying the login password is shown below:
Click on the icon in the upper left corner of the VSC-IssuingP software interface, pop-up drop-down menu, select “Password options” sub-menu of the “Change login password” menu. In the pop-up menu, select the “Change login password” menu in the “Password options” submenu, and then enter the new password in the pop-up password change dialog box, and then complete the setup, as shown below:
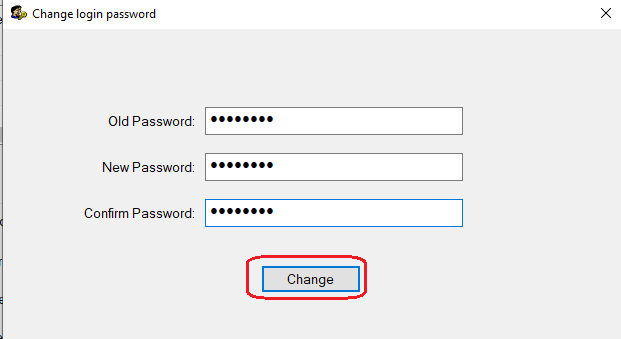
Enter the old password, new password and verify the new password, then click the “Change” button to complete the password change:
2.2 Mobile SecVSC App Installation Steps and Configuration Instructions
2.2.1 Instructions for downloading and installing the SecVSC App on mobile devices
In addition to installing the PC software, users also need to install the corresponding app on their mobile devices that they use daily, such as an iPhone or an Android phone.
Please visit the official website's SecVSC product homepage:https://www.junkai-tech.com/en/secvsc, where you can choose the corresponding mobile APP for scanning and downloading, and then follow the APP's prompts to gradually complete the installation and configuration of the SecVSC APP. The following section explains the installation of the APP on Android phones as an example, and the installation process for Apple phones is the same as that for Android phones, so it will not be repeated.
2.2.2 SecVSC App Installation Steps and Configuration Instructions for Android Phones
(1) Download the SecVSC for Personal V1.4.2 App install files:SecVSC-app-Personal-V1.4.2.apk;
(2) Install the SecVSC for Personal V1.4.2 app(.apk) into the a android phone:
 ------🡪🡪
------🡪🡪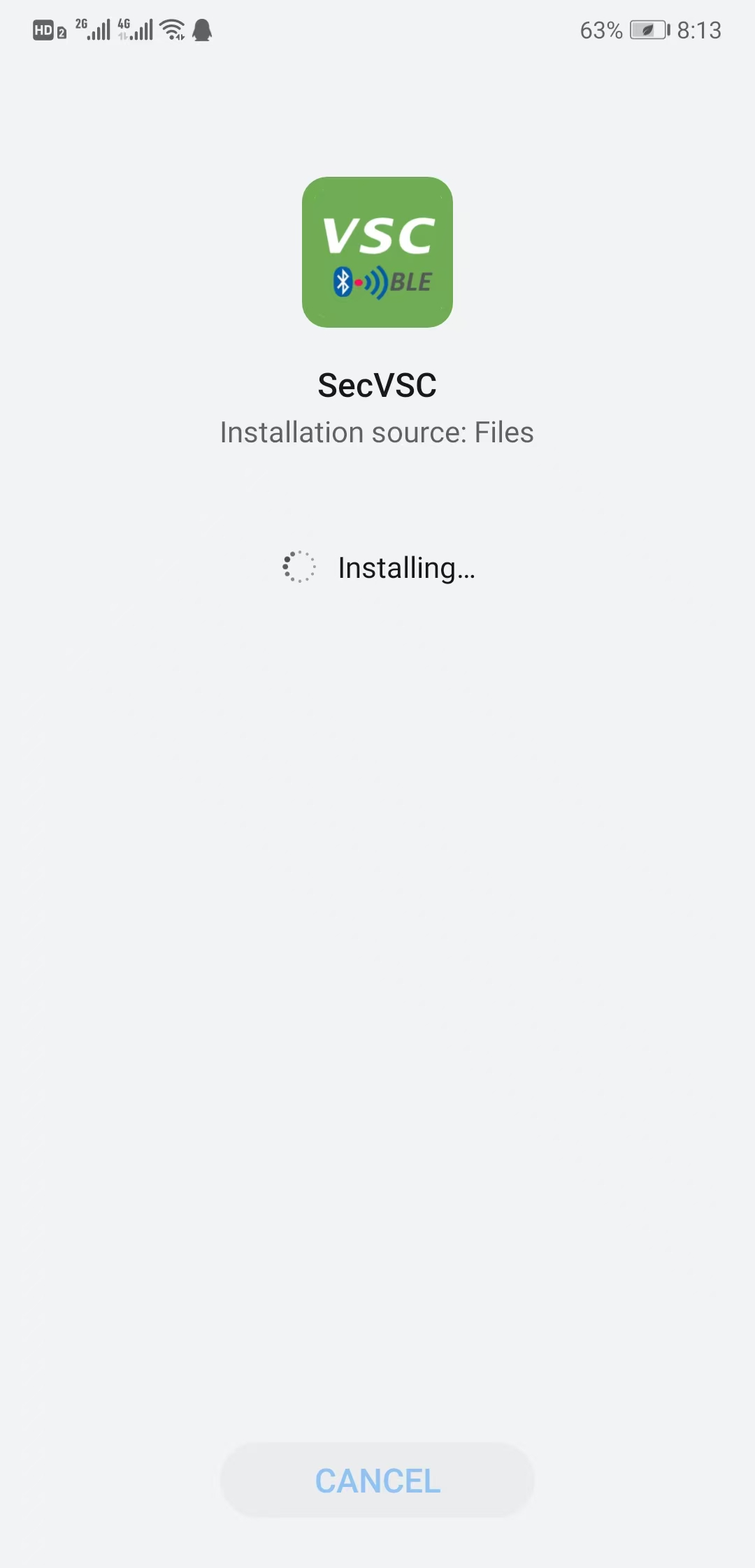
After install SecVSC for Personal V1.4.2 app success, first running the app on android phone;
Initial configuration is required for the App to run for the first time:
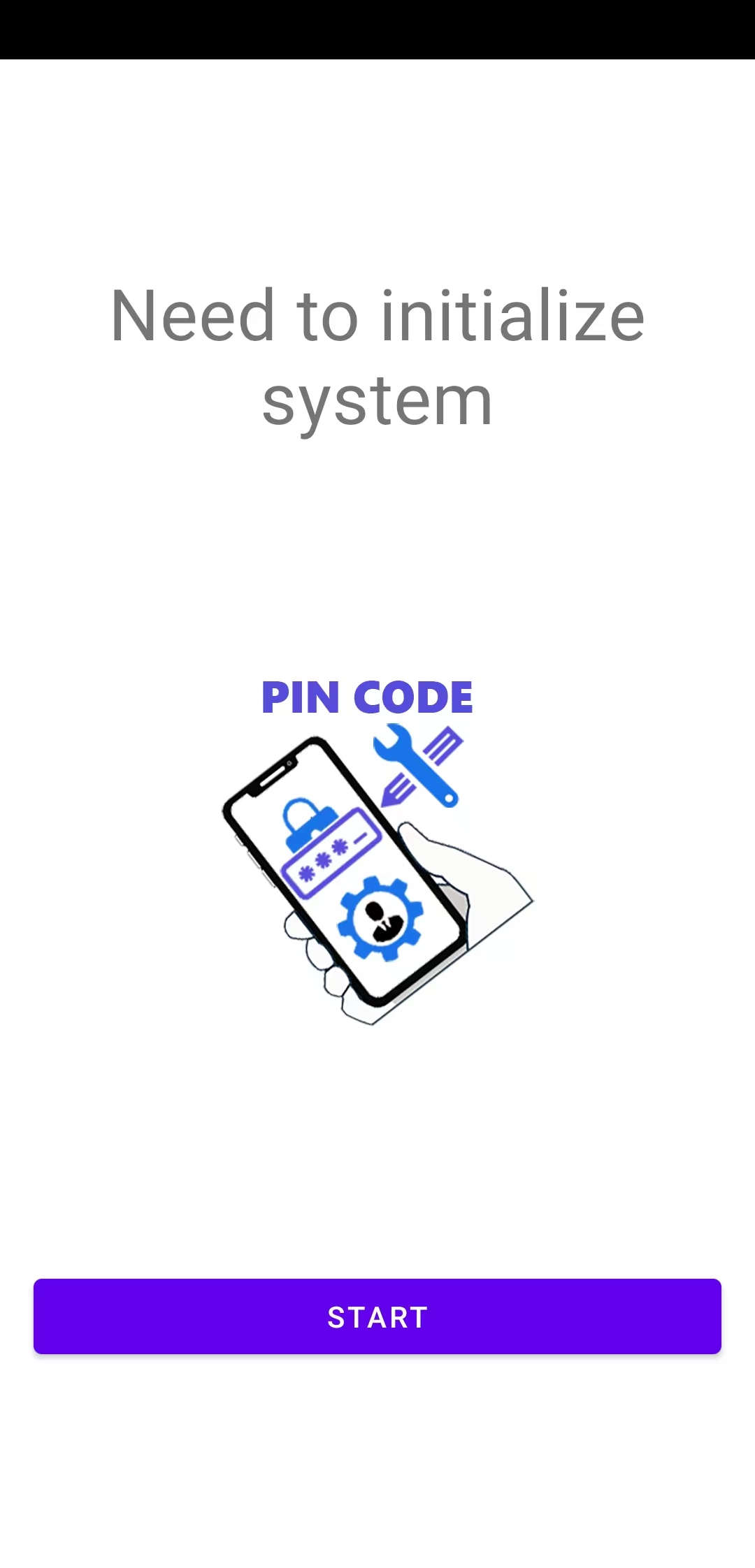
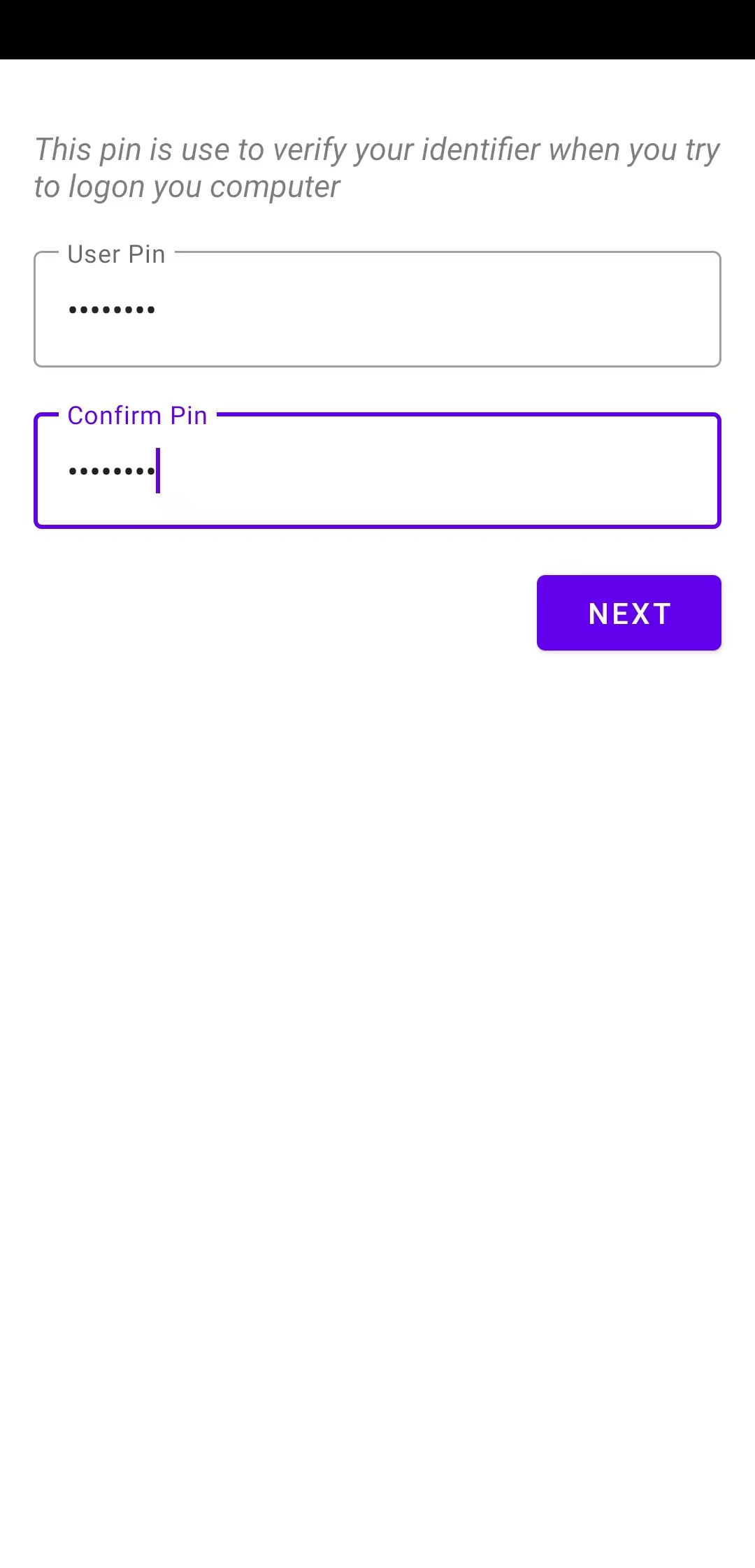
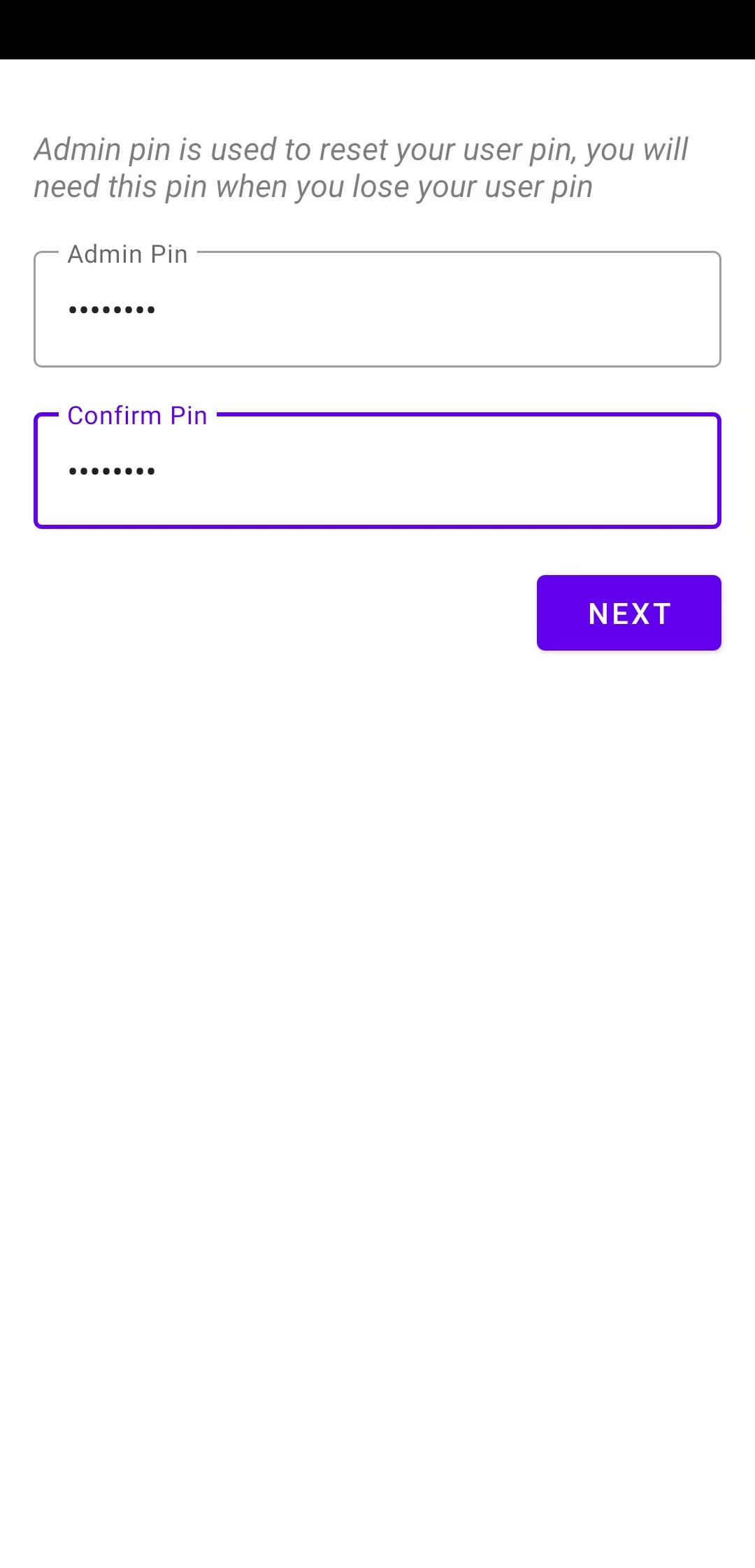
Set up an Admin PIN code for App: Admin PIN is provided to the cell phone user as the administrator password of the app, which is used to modify the user PIN of the app or reset the user PIN of the app.
Set up a User PIN code for App: User PIN is the user-level authentication password required to grant legitimate cell phone users access to SecVSC App related operations and functions, and is used for daily login access to use the functions of human-computer authentication. Users may be asked to authenticate their user PIN during computer login operations and use of the App to ensure the legitimacy and security of the operation.
Mobile users or administrators can enter the appropriate User PIN and Verify PIN, and then click “NEXT” to proceed to the next step.
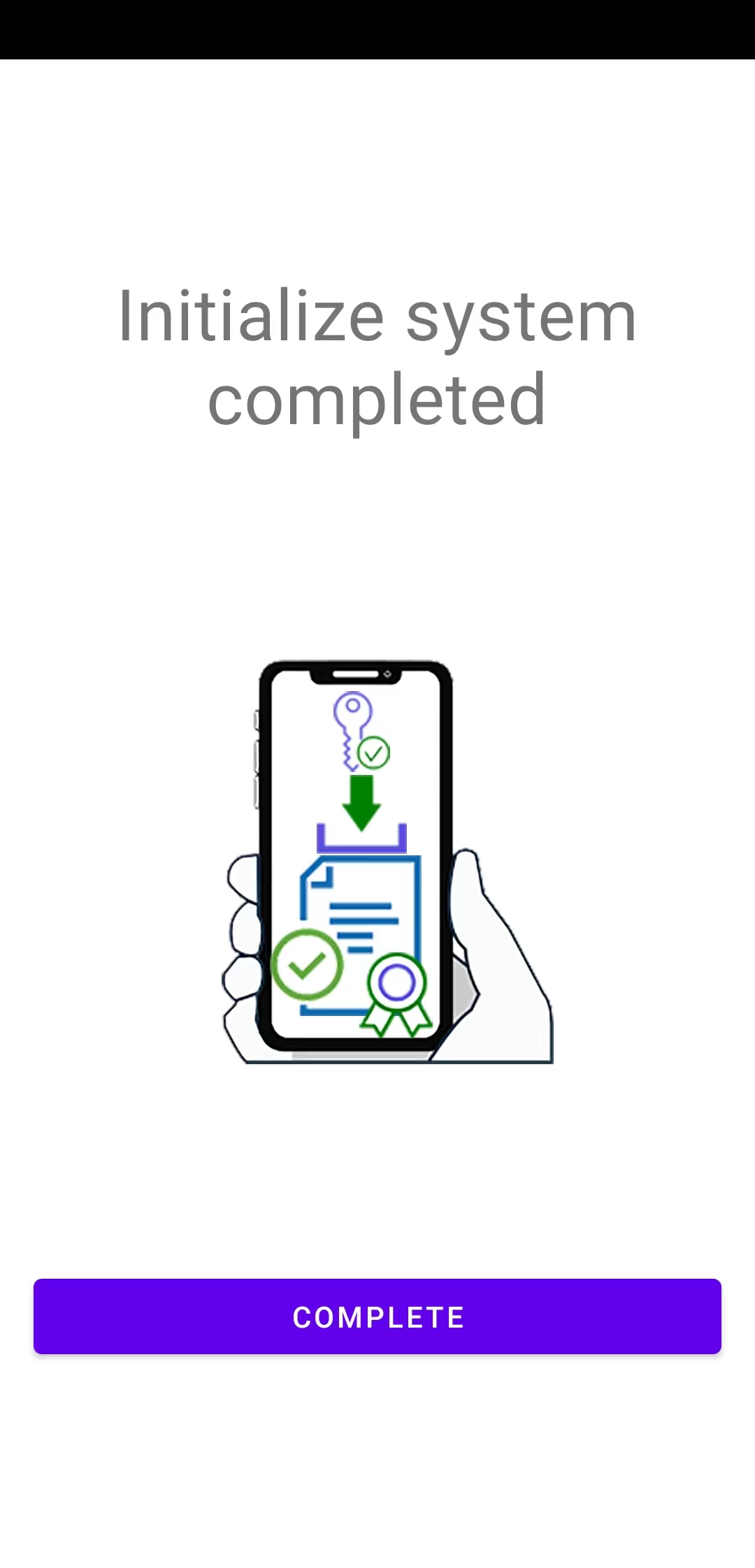
After completing the above operations, the App will pop up the initialization completion interface, click on the “COMPLETE” button to formally end the initialization configuration, enter the App main interface;
2.2.3 Connected to computer operation
Complete the initialization of the cell phone SecVSC App, if you want to use to log in to the computer, the first step is to establish a connection with the target computer, the phone will be connected to the computer and record and save the relevant computer connection parameters, the first time the connection is successful, the next time the phone is connected to the computer does not need to scan the computer QR-CODE to connect, you can directly click to select the cell phone App in the relevant You can directly click to select the relevant computer in the mobile phone app for authentication and login operation.
The procedure for connecting the mobile app to a computer for the first time is as follows:
The administrator enters the computer, logs in and opens the VSC-IssuingP certificate management tool, and displays the corresponding computer connection QR-CODE on the software interface;
Please refer to section 2.1.2 “Software Configuration Procedures and Instructions for PC” in this document for (6) connection instructions!
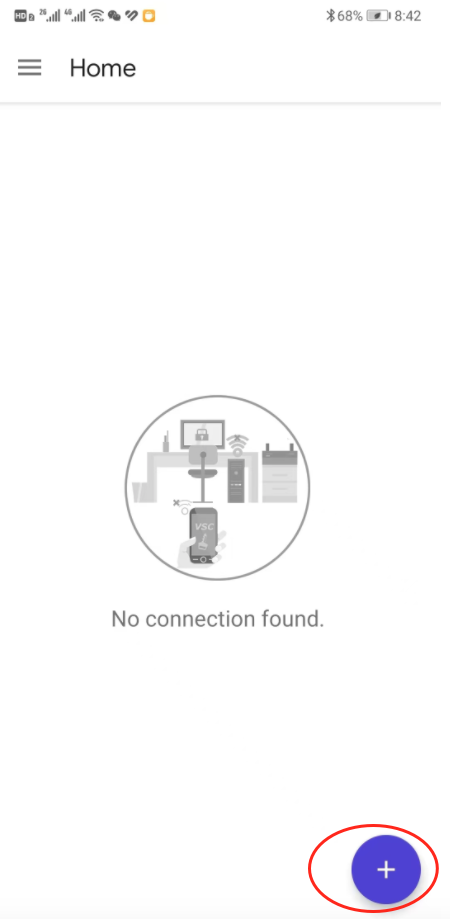
Users can open SecVSC App on their cell phone, and in the “Home” menu page, click the “+” button to activate the cell phone camera, and then point it at the computer to connect to the QR-CODE for scanning, as shown below:
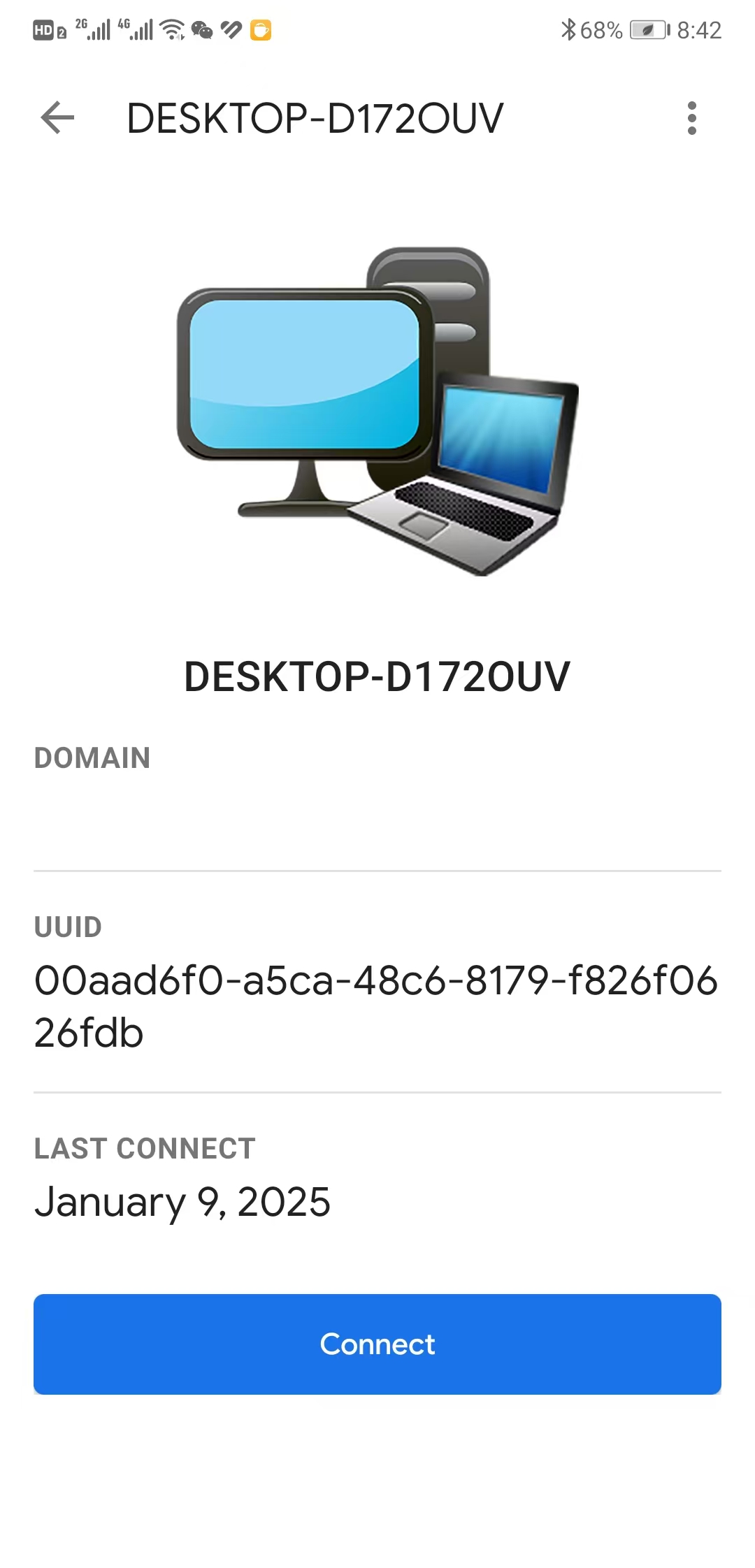
After successful scanning the phone appears on the connection page as follows:
Click the “Connect” button on the App page to connect, if the connection is successful, the App will prompt the corresponding connection error, if the connection is successful, the App page will be switched to another page (the first time you connect to the user account, you need to administrator to write the user certificate issue to the phone), the App page will switch to another page. As shown below:
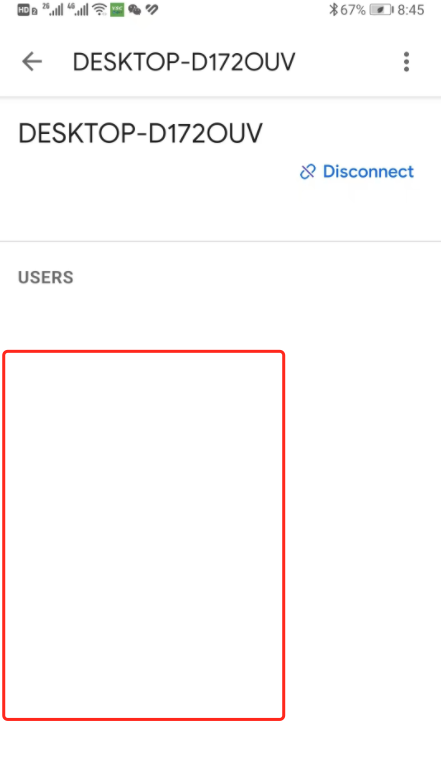
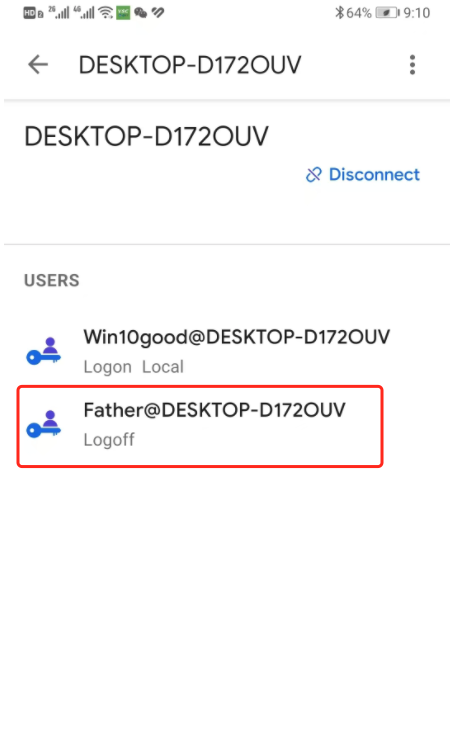
If there is no display in the red box of USERS in the above figure, it means that there is no user certificate on the cell phone device, and it is necessary to write the user certificate into the cell phone from the computer side (for details on how to issue user certificates to be written into the cell phone device, please refer to the previous section of the computer side of the operation), the following figure shows that two user certificates have already been issued to the cell phone device:
In the above page, it shows that the computer has been connected successfully, and it shows that the cell phone device has two user credentials (example), the user can click on one of the users in the “USERS” list to log in to the computer, such as the “Father@xxx-xxx” user in the above picture. User can click on one of the users in the “USERS” list to log in to the computer, such as the “Father@xxx-xxx” user in the picture above, the computer will authenticate the login request from the cell phone, and after successful authentication, run the user to log in to the computer system.
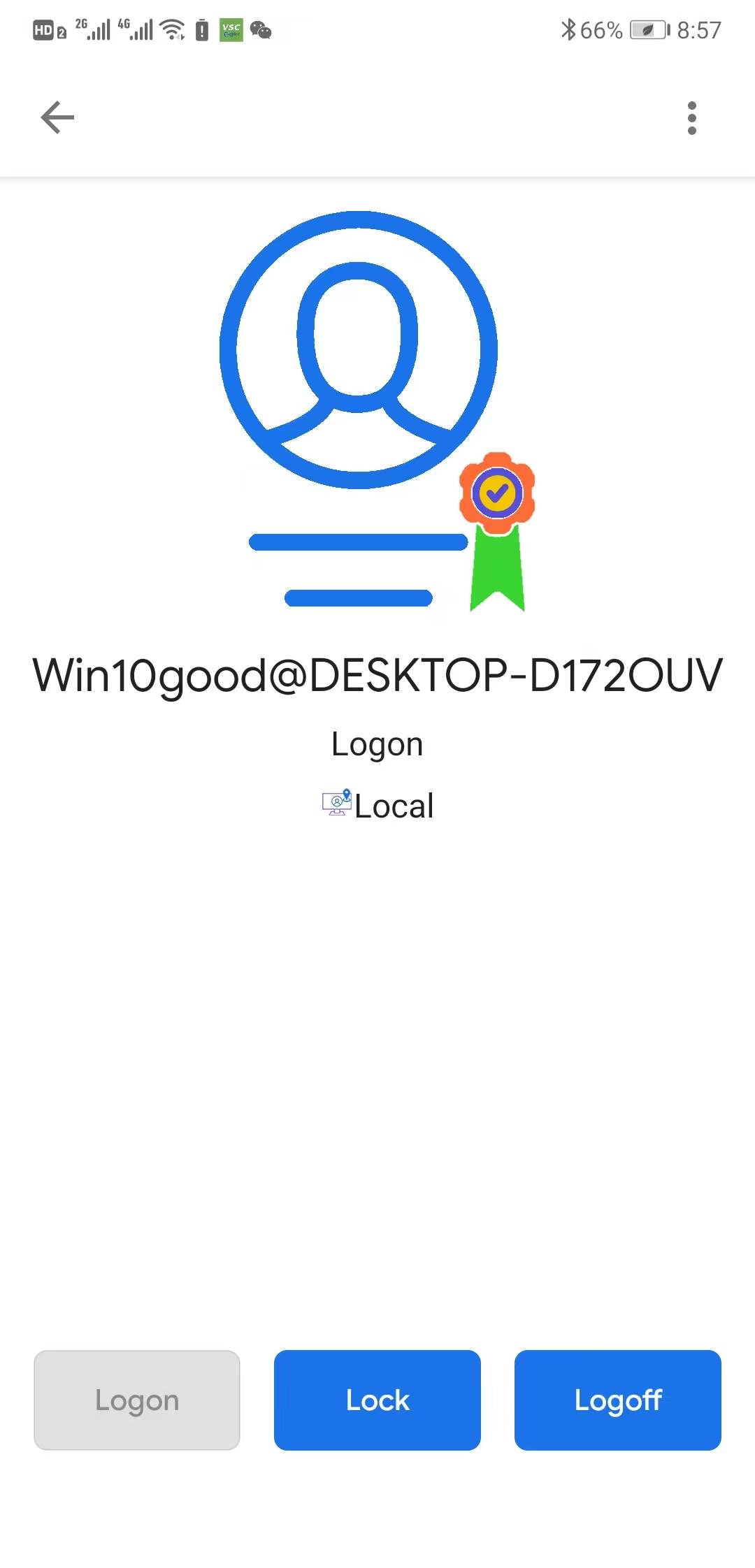
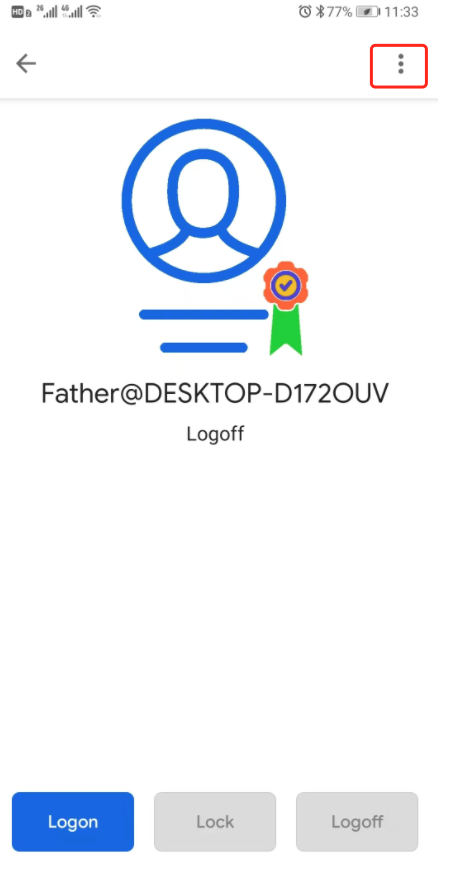
When the user has successfully logged in to the computer, the App page on the cell phone can see the user's login status and related operation functions: Lock, Logoff, etc. As shown below, Win10good users have logged in to the computer, and the cell phone can operate the Lock screen or Logoff button:
2.2.4 Mobile SecVSC App Setting Function
Click on the menu button in the upper left corner of the SecVSC App page , Lists the App's menu list, as shown below:
, Lists the App's menu list, as shown below:
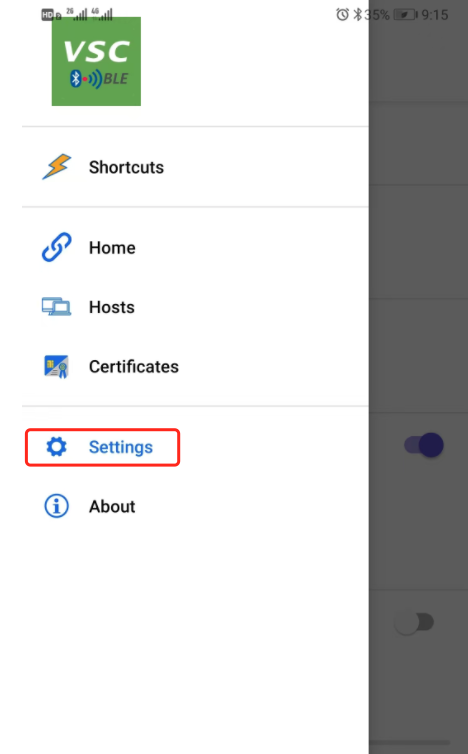
Select the “Settings” submenu in the menu list to enter the settings page of SecVSC App, as shown below:
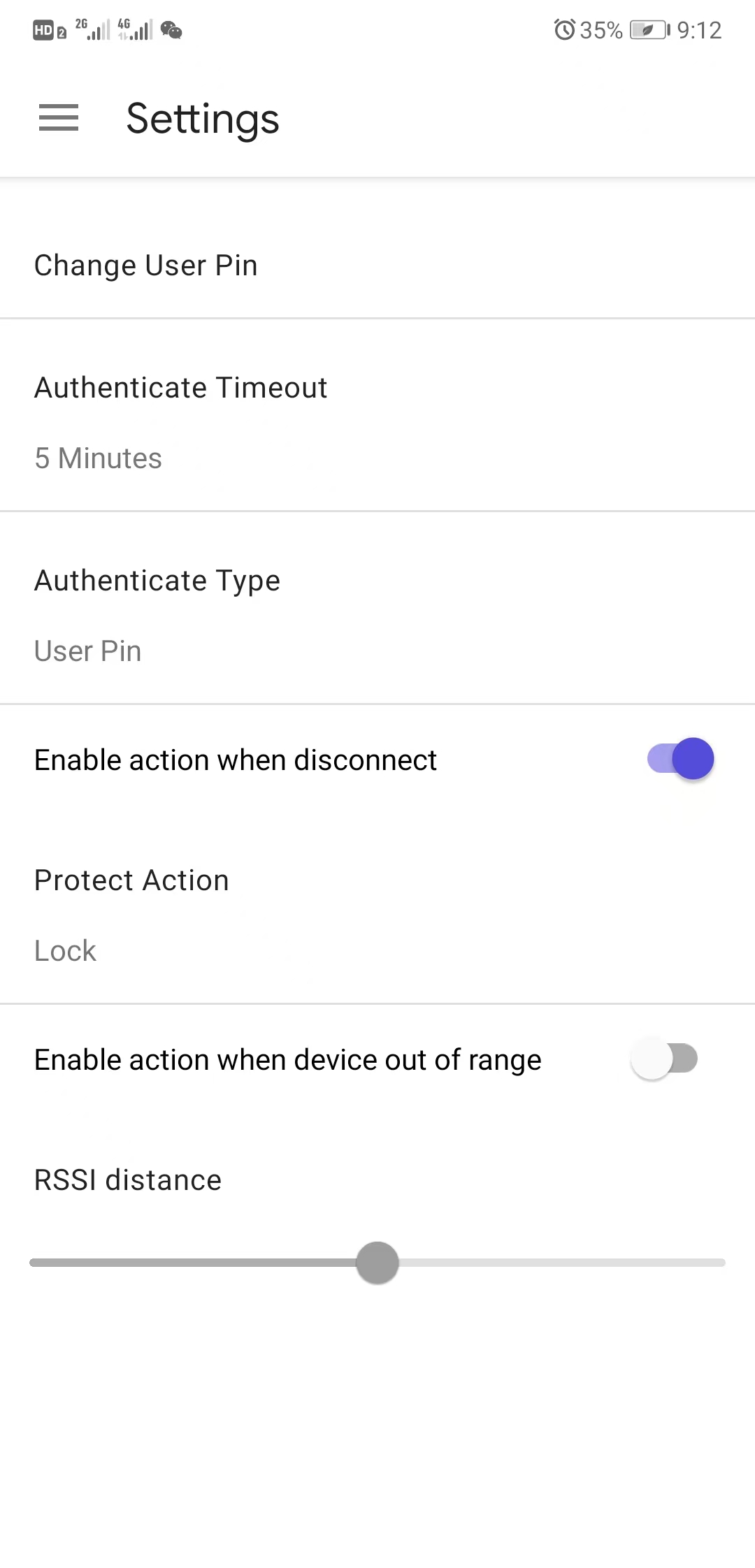
The main function of the Settings page is to provide customizable operation options for the use of the App, as well as some basic parameter setting functions, mainly including:
Change User Pin: Here you can change the user PIN, cell phone users can change the user PIN of SecVSC App from time to time;
Authenticate Timeout: The validity timeout after successful user PIN verification, you can select multiple different times (5 minutes, 1 hour, or other), such as 5 minutes, then when the phone for the user PIN authentication to maintain the authentication security validity of 5 minutes, more than 5 minutes after the last user PIN authentication is invalidated, you need to re-authentication;
Authenticate Type: Login security authentication type, refers to the security confirmation method adopted by the user when using cell phone for computer login, there are three different security confirmation methods:
| Authenticate Type | Description | Security level | |
|---|---|---|---|
| 1 | User Pin | PIN verification is required for every login, lock screen and logout operation. | Top |
| 2 | Acknowledge | Keystroke confirmation is required for each login, lock screen and logout operation. | High |
| 3 | None | No need to verify and confirm each login, lock screen and logout operation. | There is some possibility of risk in certain scenarios! |
The above three different security confirmation methods are all applied in the operation scenario of cell phone logging into computer devices, with a special note on the third security confirmation method “None”:
The “None” option is designed to meet the simplest and fastest needs of users to log in to their computer devices, eliminating the security checks of verifying User PIN and Acknowledge manual key confirmations, and directly allowing the phone to communicate with the computer inductively to realize automatic security authentication in the process of logging in to the device. The “None” option is set up so that the cell phone is very much like a car RF key, which can open the car door (logging into the computer) directly after automatically connecting to the car when it is close to the car, and this “None” option provides the convenience of logging into the computer and reduces user operation. This “None” option provides the convenience of logging in to the computer and reduces the user's operation, but carries the same risk as opening the car door with the car key:
If the “None” option is selected on the phone, and the user takes the phone to a public area, such as an office or a coffee shop, and if the person has logged on to the computer and forgets to take the phone with him or her, and the phone is next to the computer, even if the phone is in a locked state, others may access it directly through the computer (because the phone has been in a state of being connected to the computer and maintaining communication with the computer); or if the user is working with others in a room with the phone, and if the phone selects the “None” option to log on to the computer device, it may be used by others to access the computer directly. If the user is working with other people in a room with a cell phone, and the cell phone selects the “None” option to log in to the computer, others may take advantage of the cell phone's connection to the computer to log in illegally.
If the phone has the “None” option selected, there is no risk of drone-based authentication if the “None” option is selected in a confined space, or in a separate location, such as a home or hotel! Because there is no chance that anyone else can get close to the computer or cell phone, the level of security is the same as with User Pin. If the user leaves the computer with the phone, the “None” option is disabled and the computer will automatically require strong authentication.
Therefore, regarding the selection of the security confirmation method of Authenticate Type, the following selection suggestions are given below, and the actual user decides the selection by himself/herself:
| Authenticate Type | Recommended usage scenarios | Security level | |
|---|---|---|---|
| 1 | User Pin | Public areas, office areas, situations with multiple people present. | Top |
| 2 | Acknowledge | Public areas, office areas, situations with multiple people present. | High |
| 3 | None | Home, alone, fully shared public areas, unprotected trusted office environments, situations where you allow others to log in to your computer using your own account. | Middle There is a small risk that the phone is present and connected and logged in to the computer, and that others can potentially use the computer device without the phone's PIN authentication or manual confirmation. |
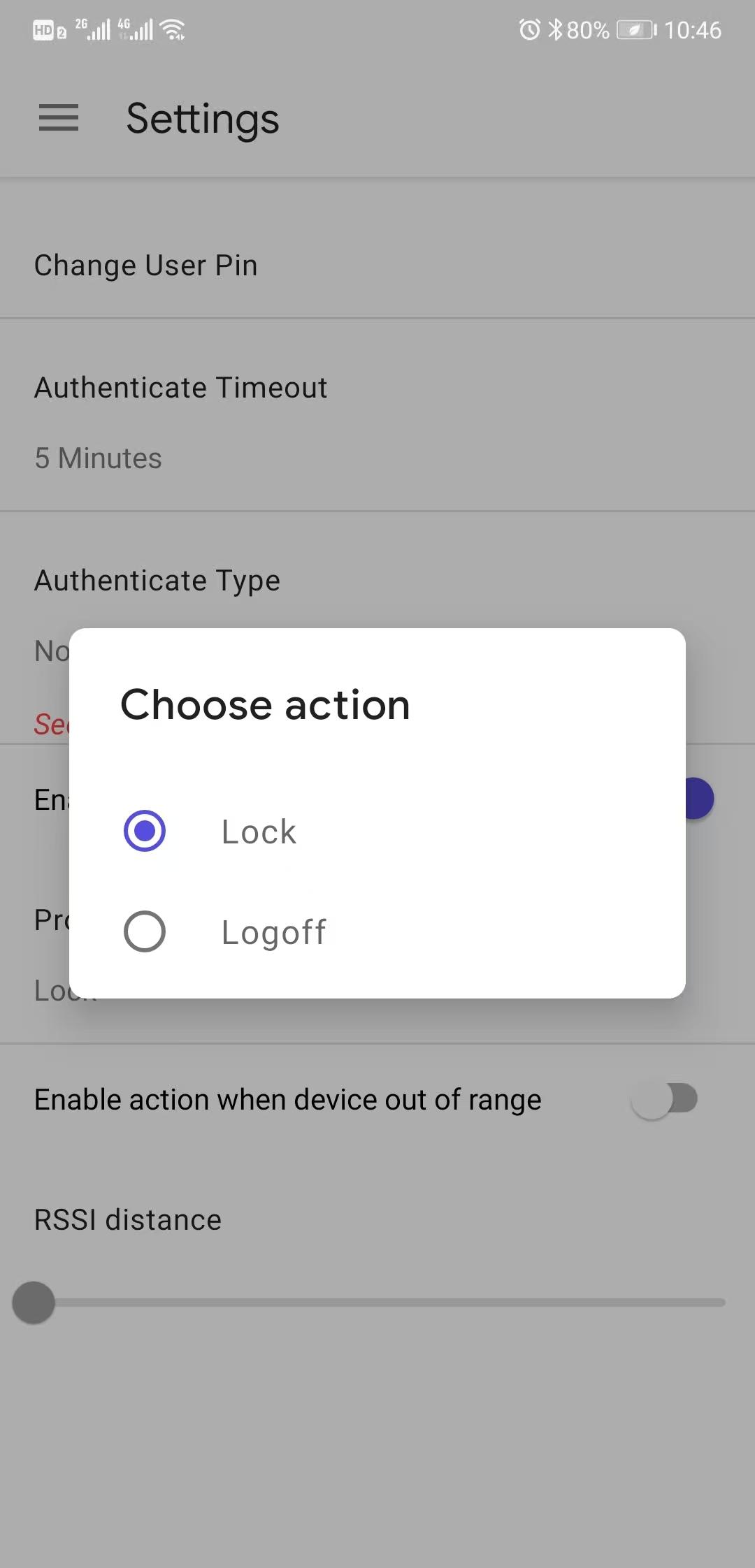
Enable action when disconnect: This option setting, if enabled, is to set what operation is triggered for the computer when the phone is disconnected from the computer, and the main operation has the following sub-options:
Lock: Lock screen, when the phone is disconnected from the computer, the computer automatically locks the screen, this operation is mainly to prevent people from leaving the computer for a period of time or forget to lock the screen, others have the opportunity to operate the computer security risks;
Logoff: Log out of the computer, when the phone is disconnected from the computer, the computer automatically logs out of the current account, this operation is mainly to prevent people from leaving the computer for a period of time or forget to lock the screen, others have the opportunity to operate the computer security risks;
Enable action when device out of range: This option setting, if enabled, allows the phone and the computer in the connection state, the phone and the computer's position distance exceeds a certain range (such as 1.5 meters, 2 meters or 3 meters, cell phone users can calibrate and set the position distance to define the relative distance value), the computer automatically locks the screen, this operation is mainly to prevent the person to leave the computer for a certain distance or to leave the line of sight to forget to lock the screen, the other person has the opportunity to Security Risks of Operating a Computer;
3.SecVSC App operational use and special features description
3.1 Introduction to the main daily operation and use
SecVSC App and computer security operations between the standard PKI technology and multi-factor security authentication, end-to-end communication also uses encrypted line protection measures, SecVSC App provides users with a safe and convenient computer login security solutions, the daily use of computers in the scenario, the user to use the SecVSC App's main operational functions are the following main operations:
| Operations | Description | Comment |
|---|---|---|
| Connect | Users can connect to specific computer devices through the App's QR-CODE scanning connection or the computer host saved in the App. | Users need to manually connect the computer before each use of the computer. |
| Disconnect | Users disconnect manually, or move away from the computer to disconnect, or just close the app to disconnect. | When the phone is disconnected from the computer, the app prompts to disconnect and allows the user to reconnect by pressing a key. |
| Logon | Once the phone is connected to the computer, it allows the user to log in to the computer device by clicking on the “Logon” button. | Users may need to be authenticated with a PIN or Acknowledgement when logging in to a computer device, as set by the user. |
| Lock | To lock the screen, users can click the “Lock” button to lock the computer screen; in addition, you can also set the Action to trigger the computer lock screen, such as disconnect. | Users may need to be authenticated with a PIN or Acknowledgement when lock a computer device, as set by the user. |
| Logoff | To log out, users can click the “Logoff” button to log out of the current computer account. | Users may need to be authenticated with a PIN or Acknowledgement when logoff a computer device, as set by the user. |
| Shutdown | Shut down the computer, the user can shut down the computer through the corresponding menu on the app, you can also set the timing conditions to shut down the computer on a regular basis. The timed shutdown feature is mainly applied to those scenarios where you need to leave the computer but still need to let the computer continue to work, such as leaving from work and letting the computer shut down automatically after three hours. | The Shutdown and Timed Shutdown menus, visible in the Properties menu of the connected computer host of the App, are divided into two types: Direct Shutdown and Timed Shutdown, and Timed Shutdown allows the user to set a certain amount of time after which the computer automatically shuts down. |
3.2 Setting up and using the Shortcuts feature
Shortcuts is an easy-to-use program designed based on smartphone sensors and system features that allows you to “shake” a key to log in or log out of your computer, making it ideal for users who need the simplest password-less login and shutdown, and other computer operations.
The procedure for adding and setting up Shortcuts is as follows:
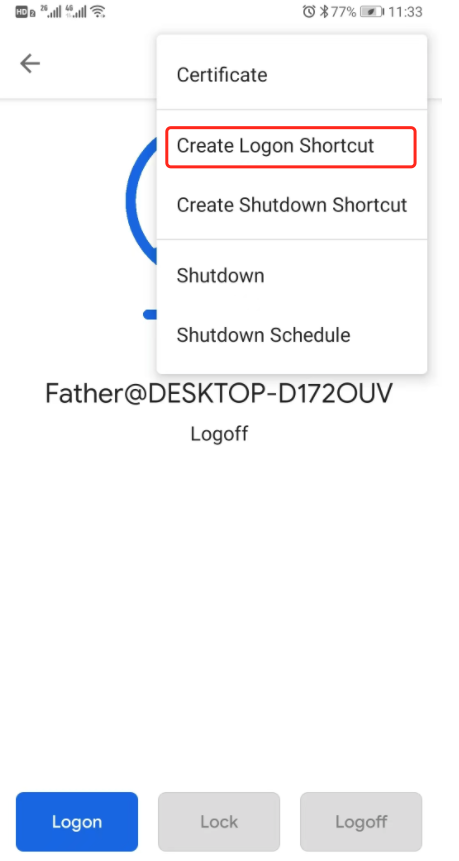
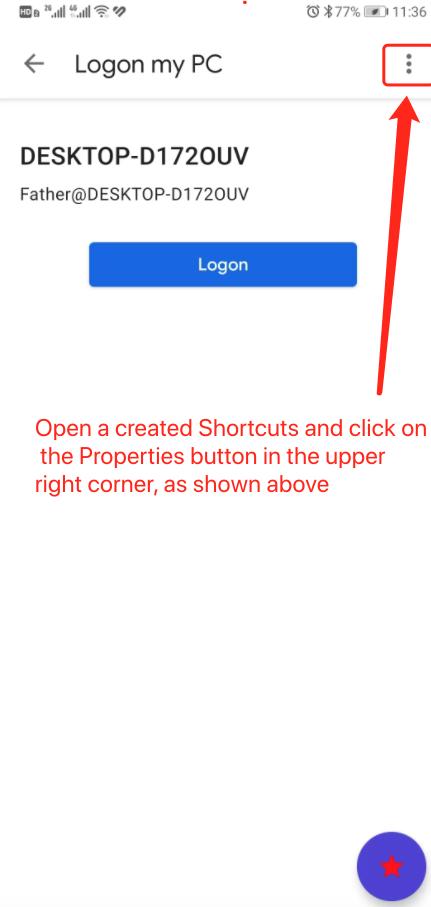
With the phone connected to the computer, enter the main interface of the computer operated by the phone, and click the “...” property menu in the upper right corner, as shown below:
In the drop-down menu, select the “Create Logon Shortcut” submenu, as shown below:
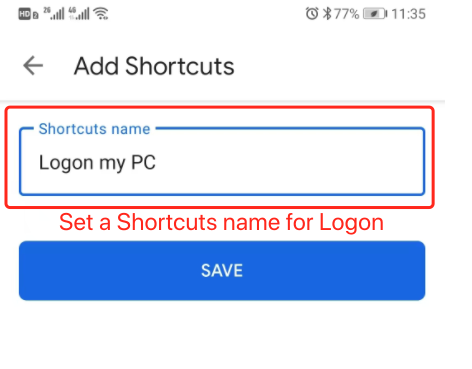
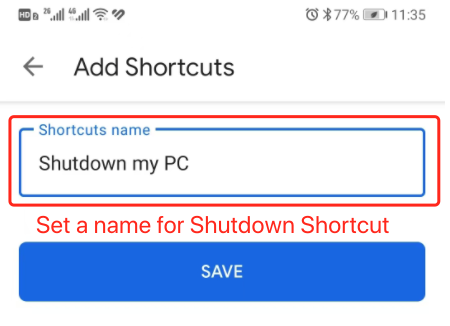
Set a Shortcuts name for Logon this PC, press “SAVE” button to create a Shortcuts:
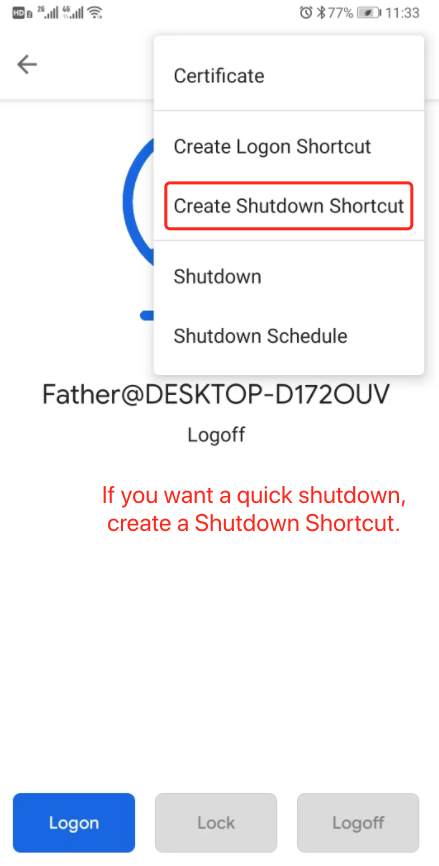
In the drop-down menu, select the “Create Shutdown Shortcut” submenu, as shown below:
Set a Shortcuts name for Shutdown this PC, press “SAVE” button to create a Shortcuts:
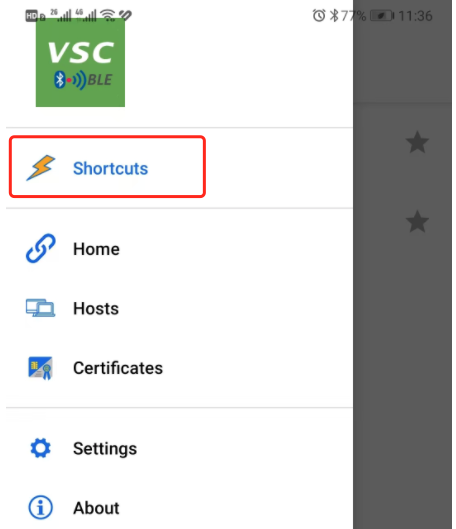
View the Shortcuts in list via “Shortcuts” menu:
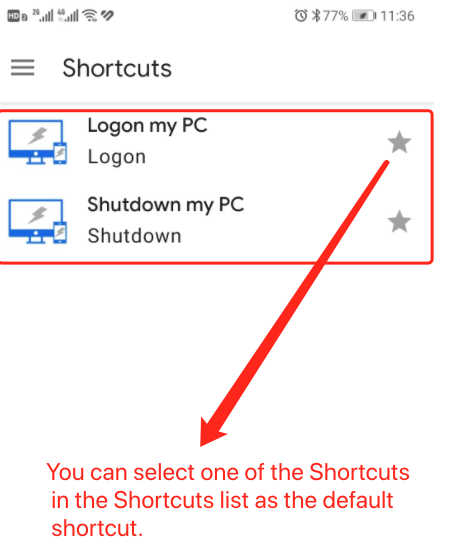
In the Shortcuts you can see all the created Shortcuts of phone:
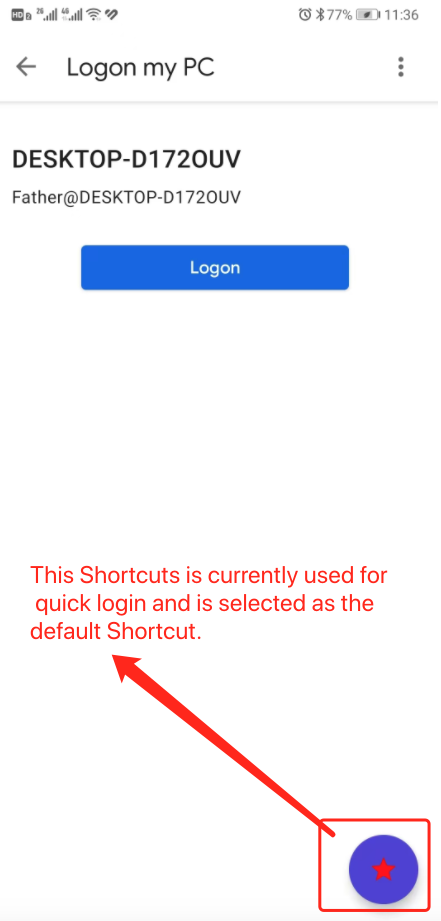
For example, use a logon shortcut as the default shortcut:
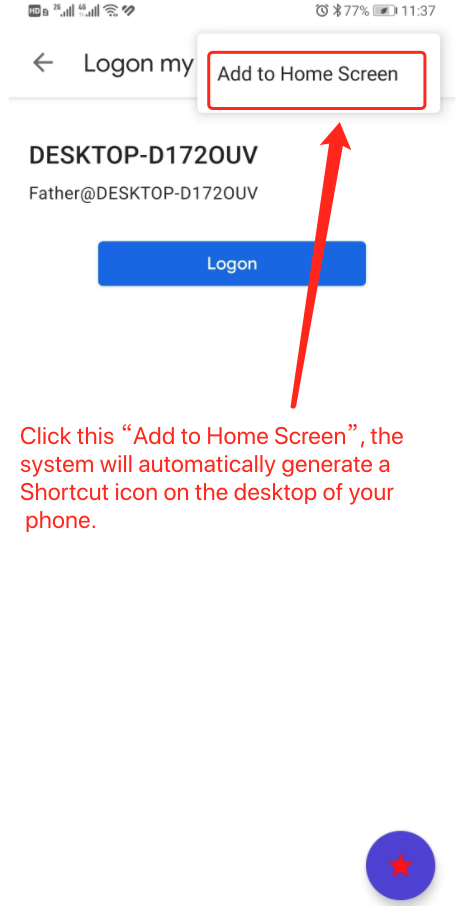
For Android smartphones, there is also a special feature for faster one-click login or shutdown with the following settings:
Click the “Add to Home Screen” menu, the phone system will automatically generate a Shortcut icon on the phone desktop page:
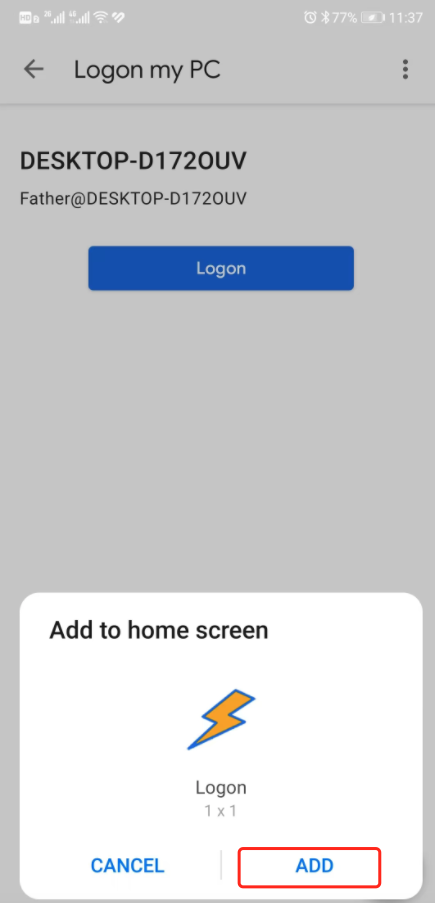
Afterwards, the app will pop up a “ADD” dialog box to add to the desktop, click on the “ADD”, you can Shortcut directly on the phone screen desktop to generate a lightning bolt logo of the one-key run icon.
The phone's desktop screen will display the relevant added Shortcut icon, such as the Logon Shortcut icon for one-click login to the computer, so that the user does not need to enter the app, directly click on this desktop Shortcut icon, you can log in to the computer, very fast and convenient.
Similarly, the desktop Shortcut icon for one-click shutdown is also available and users can directly click on it to perform the shutdown operation.
In addition, multiple different Shortcuts can be created on the phone, which can be created for different logged-in users; also, multiple one-click desktop Shortcut icons can be created on a single phone as well.